A
Alexander Schnabl
6
Workflows
Workflows by Alexander Schnabl

Free advanced
Audit SharePoint Online external sharing and anonymous links with Microsoft Graph
Audit external sharing in SharePoint to ensure compliance This workflow audits your SharePoint Online environment for...
A
Alexander Schnabl Document Extraction
6 Jan 2026
2
0
Free advanced
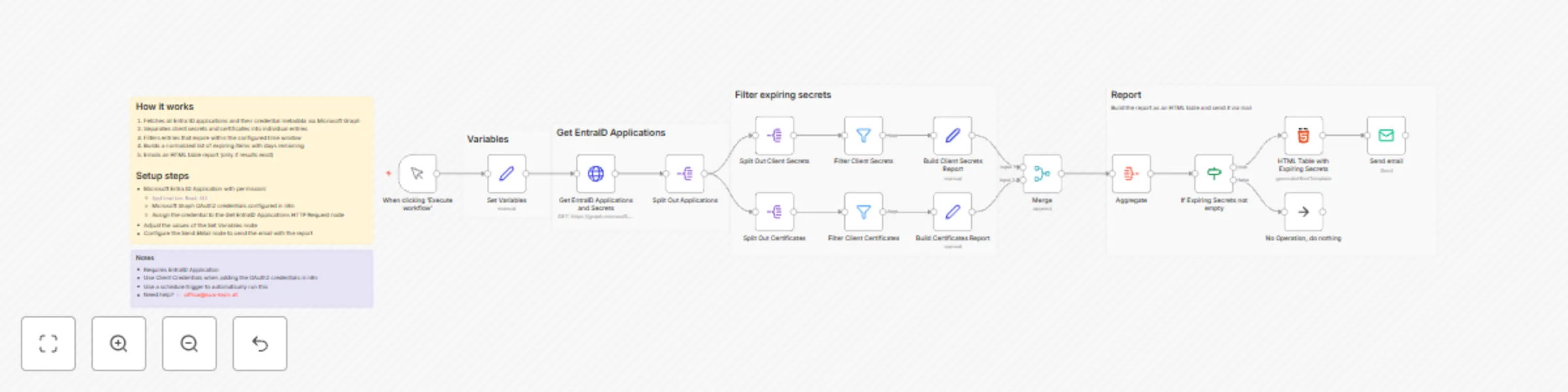
Email reports on expiring Microsoft Entra ID app secrets and certificates with Microsoft Graph
Monitor expiring EntraID application secrets and notify responsible Stay ahead of credential expirations by automatic...
A
Alexander Schnabl DevOps
2 Jan 2026
117
0
Free advanced
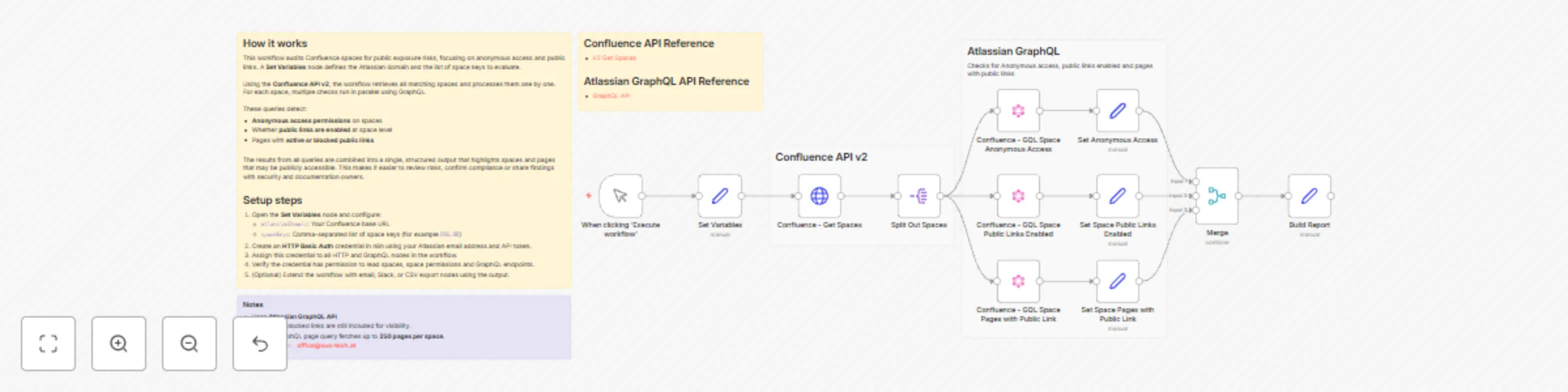
Audit Confluence space permissions and public links for compliance
Audit permissions in Confluence to ensure compliance This workflow scans selected Confluence spaces for public exposu...
A
Alexander Schnabl SecOps
28 Dec 2025
7
0
Free advanced
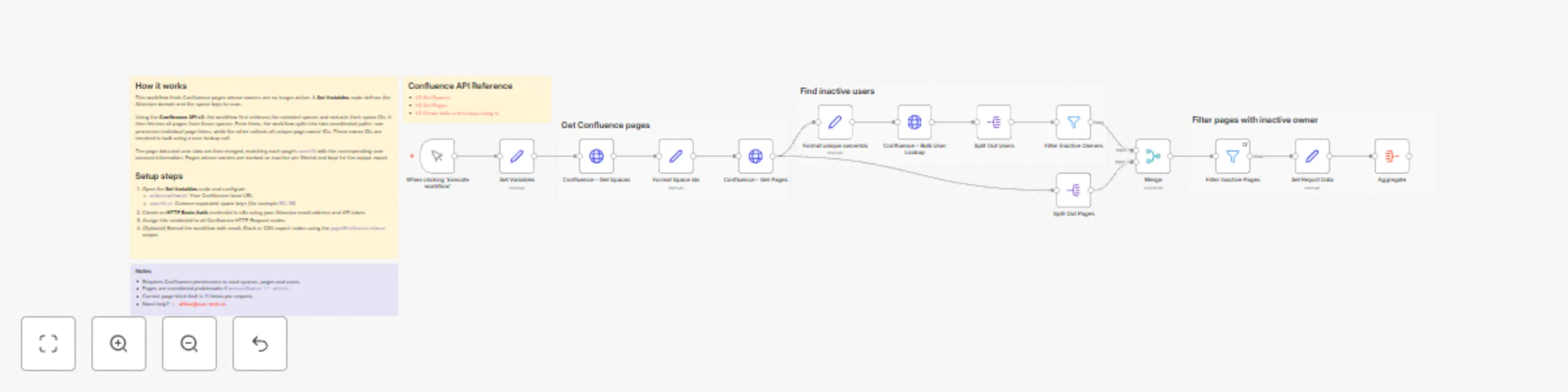
Scan Confluence pages with the REST API for inactive page owners
Scan Confluence pages for inactive page owners This workflow scans selected Confluence spaces , resolves page ownersh...
A
Alexander Schnabl Document Extraction
28 Dec 2025
5
0
Free advanced
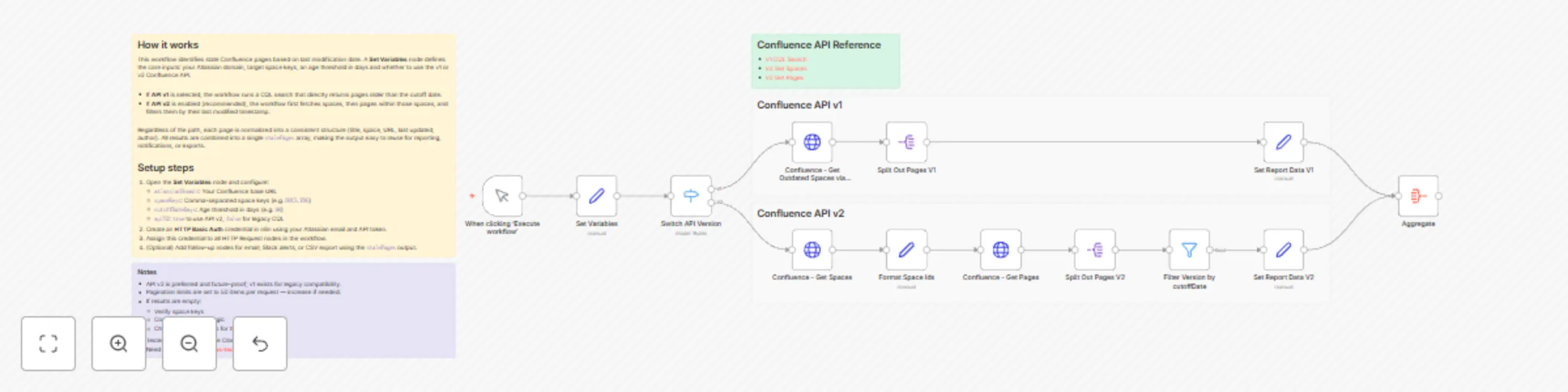
Generate stale page reports for Confluence spaces with REST API v1 and v2
Report stale pages in Confluence This workflow generates a stale page report for Confluence spaces, helping teams kee...
A
Alexander Schnabl Document Extraction
28 Dec 2025
4
0

Free advanced
Collect star rating feedback with self-contained HTML forms and data tables
Customer Feedback Survey This n8n template lets you collect lightweight customer feedback through a responsive HTML f...
A
Alexander Schnabl Support Chatbot
16 Oct 2025
238
0