Score DNS threats with VirusTotal, Abuse.ch, HashiCorp Vault and Gemini
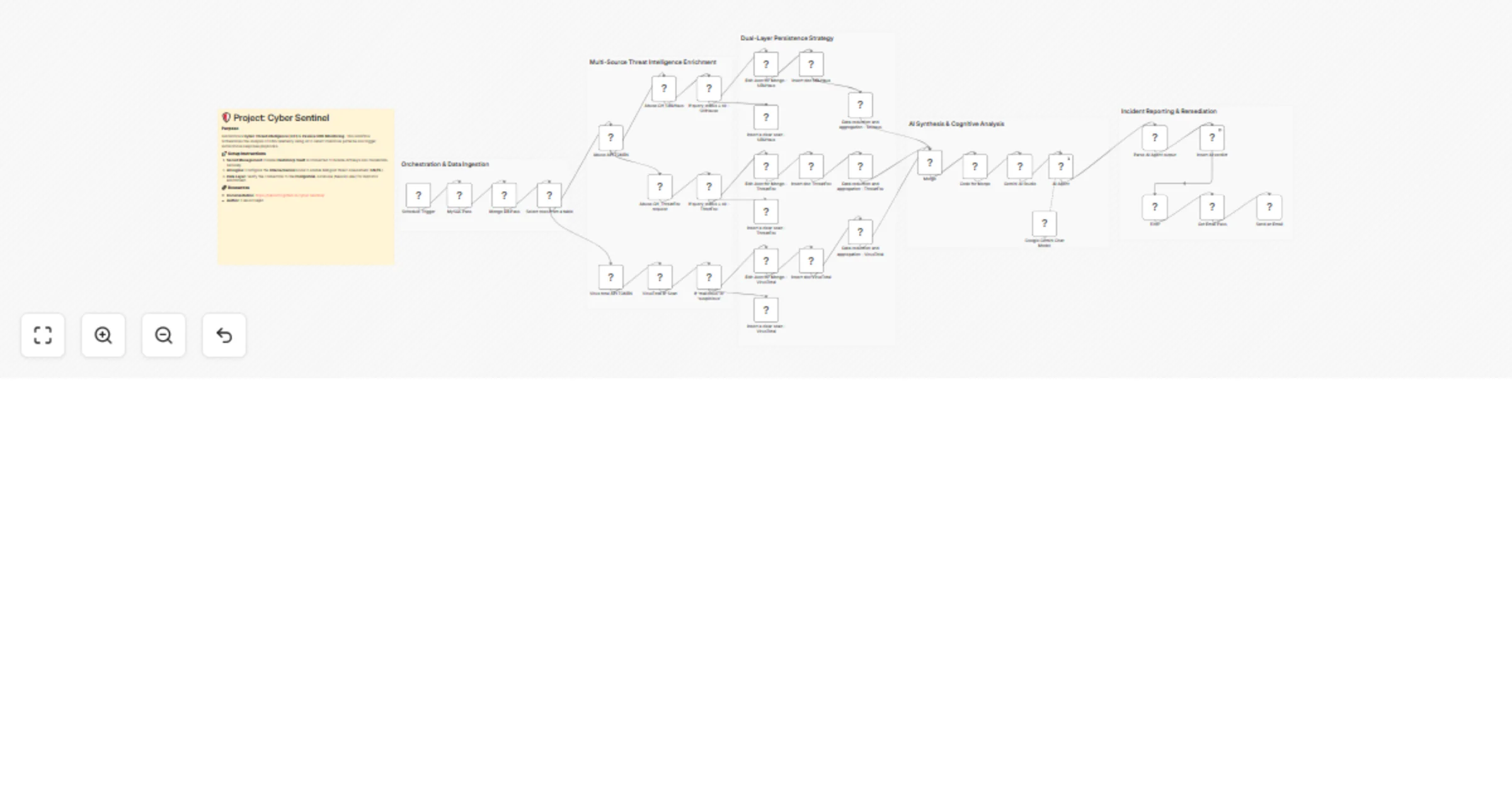
Workflow preview


 Early Deal
Early DealDISCOUNT 20%

Overview
Stop fighting alerts and start orchestrating intelligence.
This workflow is a complete ecosystem designed to combat network threats in real-time. It transforms raw DNS logs into structured knowledge, leveraging Artificial Intelligence to make decisions that previously required hours of manual work by a SOC analyst. Real-World Problems it Solves:
Manual Threat Analysis: Automates the process of verifying suspicious domains and IP addresses across multiple CTI sources simultaneously.
Security Credential Management: Eliminates the risk of API key leaks through native integration with HashiCorp Vault.
Alert Fatigue: Thanks to built-in filtering logic, the system only notifies you when the AI Threat Score exceeds 5 (Malicious/Critical).
Data Fragmentation: Consolidates data from multiple CTI providers into a single, cohesive technical report.
Core System Components:
The workflow manages and communicates with the following elements of your infrastructure:
Traffic Capture: Monitors passive DNS traffic to identify new Indicators of Compromise (IoCs).
Secret Engine: HashiCorp Vault provides database credentials and API tokens dynamically during workflow execution.
Intelligence Layer: Features three independent scanning branches: VirusTotal, Abuse_URLhaus, and Abuse_ThreatFox.
AI Brain: Google Gemini AI acts as a "Senior Security Analyst," correlating data and generating verdicts in both English and Polish.
Automated Response: An email notification system triggered exclusively for confirmed high-risk threats.
Release v1.0.0 Highlights
This release (available on https://github.com/lukaszFD/cyber-sentinel/releases) marks the first fully stable production-ready version of the system.
Key features of this release:
Full Ansible Orchestration: The entire stack—including Nginx, Vault, databases, and n8n—is deployed automatically using Ansible playbooks.
Infrastructure as Code (IaC): Secure deployment based on Ansible Vault, requiring only the population of credentials and the presence of a .vault_pass file.
Production-Ready: The system has been rigorously tested for stability in both Debian (Proxmox) and Raspberry Pi 5 environments.
Documentation : https://lukaszfd.github.io/cyber-sentinel/