Run weekly WAF security audits with WAFtester and Slack alerts
Workflow preview

$20/month : Unlimited workflows
2500 executions/month

THE #1 IN WEB SCRAPING
Scrape any website without limits
HOSTINGER  Early Deal
Early Deal
DISCOUNT 20% Try free
 Early Deal
Early DealDISCOUNT 20%
Self-hosted n8n
Unlimited workflows - from $4.99/mo

#1 hub for scraping, AI & automation
6000+ actors - $5 credits/mo
Overview
What it does
Automated weekly WAF security assessments with Slack reporting. Detects your WAF vendor, runs a security assessment, grades your protection, and alerts your team when the grade drops below threshold.
About WAFtester
WAFtester is an open-source CLI for testing Web Application Firewalls. It ships 27 MCP tools, 2,800+ attack payloads across 18 categories (SQLi, XSS, SSRF, SSTI, command injection, XXE, and more), detection signatures for 26 WAF vendors and 9 CDNs, and enterprise-grade assessment with F1/MCC scoring and letter grades (A+ through F).
- GitHub: github.com/waftester/waftester
- Docs: Installation | Examples | Commands
Who it's for
- Security teams needing continuous WAF monitoring
- DevOps engineers tracking WAF configuration drift
- Compliance teams requiring regular security assessments
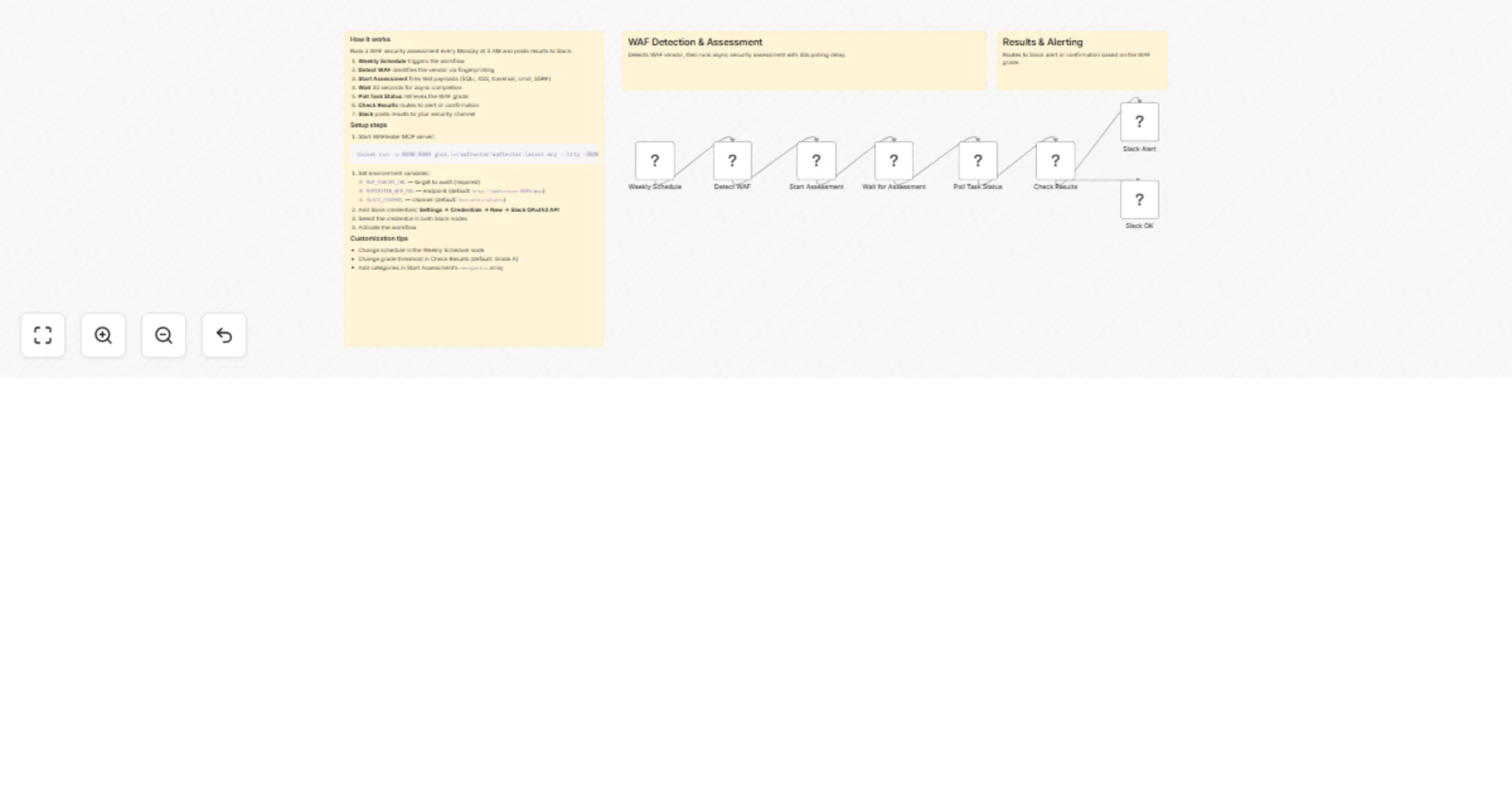
How it works
The workflow has seven nodes:
- Weekly Schedule — Triggers every Monday at 3 AM (configurable)
- Detect WAF — Calls WAFtester's
detect_waftool to fingerprint the WAF vendor and CDN - Start Assessment — Launches an async
assesstask testing SQLi, XSS, traversal, cmdi, and SSRF - Wait — Pauses to let the assessment run
- Poll Results — Calls
get_task_statusto retrieve completed results - Check Results — Routes based on the WAF grade (pass if "A" or better, fail otherwise)
- Slack (Pass/Fail) — Posts a summary to your Slack channel with grade, detection rate, and bypass count
How to set up
- Start WAFtester MCP server:
docker run -p 8080:8080 ghcr.io/waftester/waftester:latest mcp --http :8080 - Set environment variables:
WAF_TARGET_URL(required),WAFTESTER_MCP_URL,SLACK_CHANNEL - Add Slack OAuth2 credentials and select them in both Slack nodes
- Activate the workflow
Alternatively, use the included docker-compose.yml to run both n8n and WAFtester together.
Requirements
| Requirement | Details |
|---|---|
| WAFtester MCP server | Docker image (ghcr.io/waftester/waftester:latest) or binary install |
| Slack | Workspace with OAuth2 bot credentials |
| Authorization | Only test targets you have explicit written permission to test |
How to customize
- Adjust schedule in the Weekly Schedule node
- Change grade threshold in the Check Results node
- Add attack categories in Start Assessment's
categoriesarray - Swap Slack for email, Teams, or any n8n notification node