Detect and route gameplay security anomalies with GPT-4o, Slack and Sheets
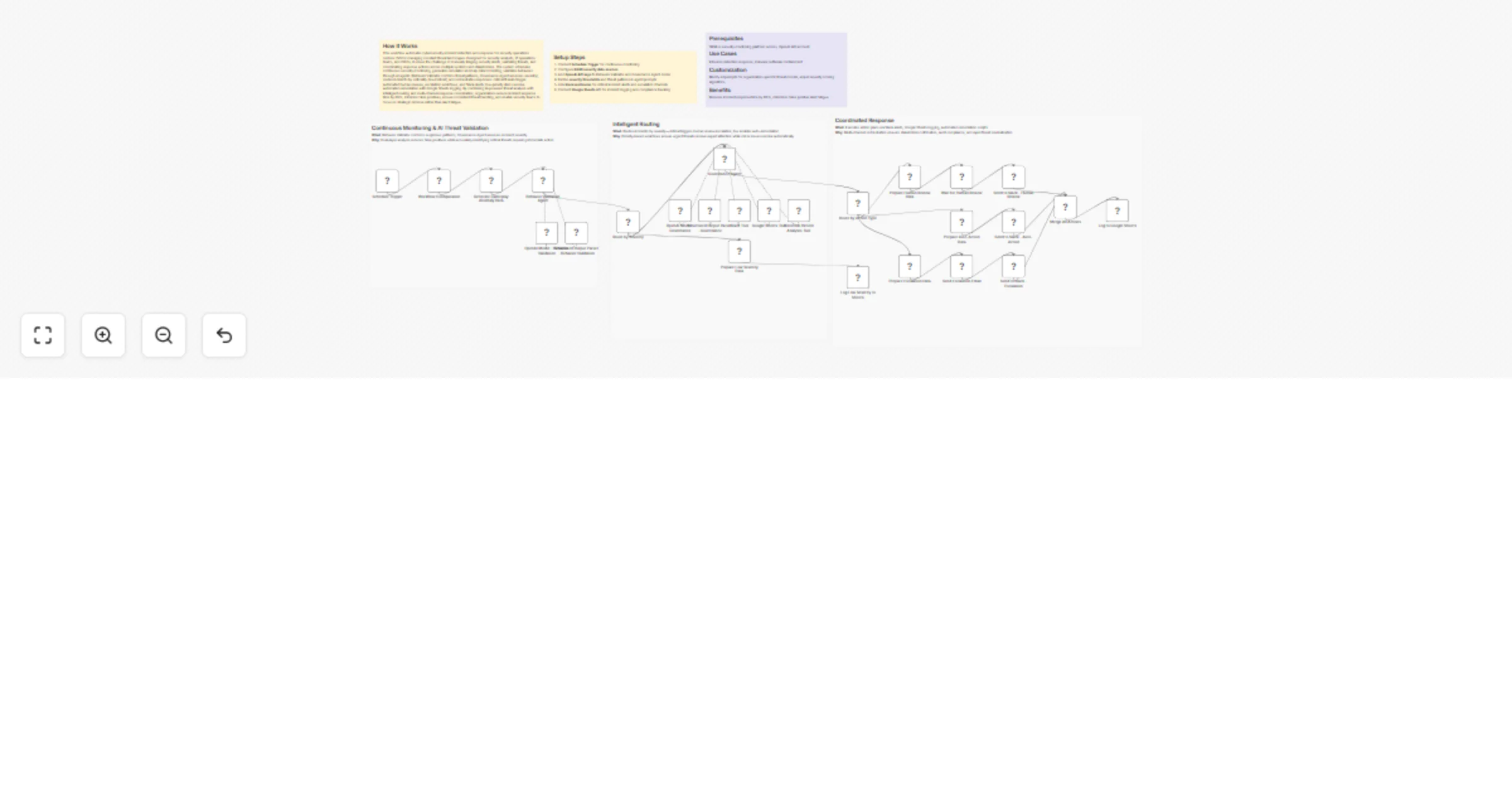
Workflow preview


 Early Deal
Early DealDISCOUNT 20%

Overview
How It Works
This workflow automates cybersecurity incident detection and response for security operations centers (SOCs) managing constant threat landscapes. Designed for security analysts, IT operations teams, and CISOs, it solves the challenge of manually triaging security alerts, validating threats, and coordinating response actions across multiple systems and stakeholders. The system schedules continuous security monitoring, generates simulated anomaly data for testing, validates behaviors through AI agents (Behavior Validator confirms threat patterns, Governance Agent assesses severity), routes incidents by criticality (low/critical), and orchestrates responses: critical threats trigger automated human reviews, escalation workflows, and Slack alerts; low-priority items receive automated remediation with Google Sheets logging. By combining AI-powered threat analysis with intelligent routing and multi-channel response coordination, organizations reduce incident response time by 80%, minimize false positives, ensure consistent threat handling, and enable security teams to focus on strategic defense rather than alert fatigue.
Setup Steps
- Connect Schedule Trigger for continuous monitoring
- Configure SIEM/security data sources
- Add OpenAI API keys to Behavior Validator and Governance Agent nodes
- Define severity thresholds and threat patterns in agent prompts
- Link Slack webhooks for critical incident alerts and escalation channels
- Connect Google Sheets API for incident logging and compliance tracking
Prerequisites
SIEM or security monitoring platform access, OpenAI API account
Use Cases
Intrusion detection response, malware outbreak containment
Customization
Modify AI prompts for organization-specific threat models, adjust severity scoring algorithms
Benefits
Reduces incident response time by 80%, minimizes false positive alert fatigue