Detect and route cybersecurity threats with SIEM, Slack, email and PagerDuty
Workflow preview

$20/month : Unlimited workflows
2500 executions/month

THE #1 IN WEB SCRAPING
Scrape any website without limits
HOSTINGER  Early Deal
Early Deal
DISCOUNT 20% Try free
 Early Deal
Early DealDISCOUNT 20%
Self-hosted n8n
Unlimited workflows - from $4.99/mo

#1 hub for scraping, AI & automation
6000+ actors - $5 credits/mo
Overview
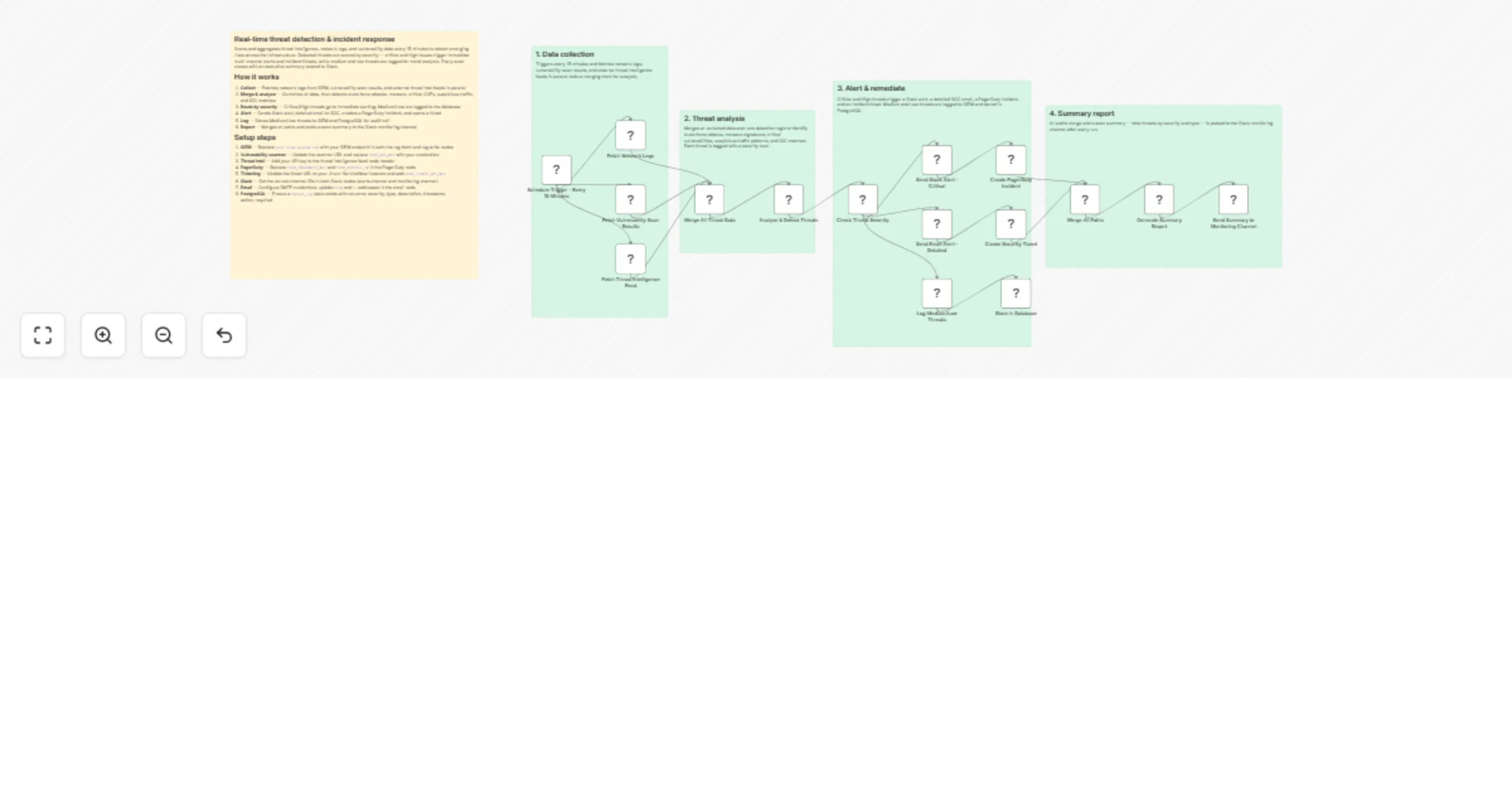
This n8n workflow proactively scans and aggregates threat intelligence, network logs, and vulnerability data every 15 minutes to detect emerging risks across the infrastructure. It analyzes anomalies, correlates indicators, assigns severity, triggers critical alerts, and generates executive-ready summaries—enabling security teams to act before threats escalate.
How it works
- Collect — Fetches network logs from SIEM, vulnerability scan results, and external threat intel feeds in parallel
- Merge & analyze — Combines all data, then detects brute force attacks, malware, critical CVEs, suspicious traffic, and IOC matches
- Route by severity — Critical/High threats go to immediate alerting; Medium/Low are logged to the database
- Alert — Sends Slack alert, detailed email to SOC, creates a PagerDuty incident, and opens a ticket
- Log — Stores Medium/Low threats to SIEM and PostgreSQL for audit trail
- Report — Merges all paths and posts a scan summary to the Slack monitoring channel
Setup steps
- SIEM — Replace
your-siem-system.comwith your SIEM endpoint in both the log fetch and log write nodes - Vulnerability scanner — Update the scanner URL and replace
YOUR_API_KEYwith your credentials - Threat intel — Add your API key to the threat intelligence feed node header
- PagerDuty — Replace
YOUR_PAGERDUTY_KEYandYOUR_SERVICE_IDin the PagerDuty node - Ticketing — Update the ticket URL to your Jira or ServiceNow instance and add
YOUR_TICKET_API_KEY - Slack — Set the correct channel IDs in both Slack nodes (alerts channel and monitoring channel)
- Email — Configure SMTP credentials; update
fromandtoaddresses in the email node - PostgreSQL — Ensure a
threat_logtable exists with columns: severity, type, description, timestamp, action_required
Industries That Benefit
- Enterprise IT/SOC: Scale threat detection without alert fatigue.
- MSP/MSSP: Offer proactive monitoring to clients with automated reporting.
- Finance & Banking: Meet FFIEC and PCI DSS continuous monitoring requirements.
- Healthcare: Detect ransomware precursors before patient data is locked.
- Critical Infrastructure (OT): Bridge IT/OT visibility with unified alerting.
Prerequisites
- SIEM with API access (Splunk, QRadar, ELK)
- Vulnerability scanner API (Qualys, Nessus, OpenVAS)
- Threat intelligence feed (OTX, MISP, commercial)
- n8n instance with Schedule, HTTP Request, Slack, and Database nodes
- Slack workspace, SMTP, or Twilio for notifications
- ITSM system (Jira, ServiceNow) with create permission
Modification Options
- Add UEBA (User Entity Behavior Analytics) integration.
- Integrate with SOAR for auto-containment on Critical alerts.
- Enable geo-mapping of malicious IPs.
- Add CVE trend dashboard via Grafana export.
- Trigger on-demand scans via webhook (e.g., post-pen-test).
- Export to security data lake for ML training.
Explore More Proactive Security Automations: Contact us to build AI-driven threat hunting, automated patching, and zero-trust enforcement workflows with n8n.