Automate cybersecurity incident response with Claude AI, VirusTotal and Slack
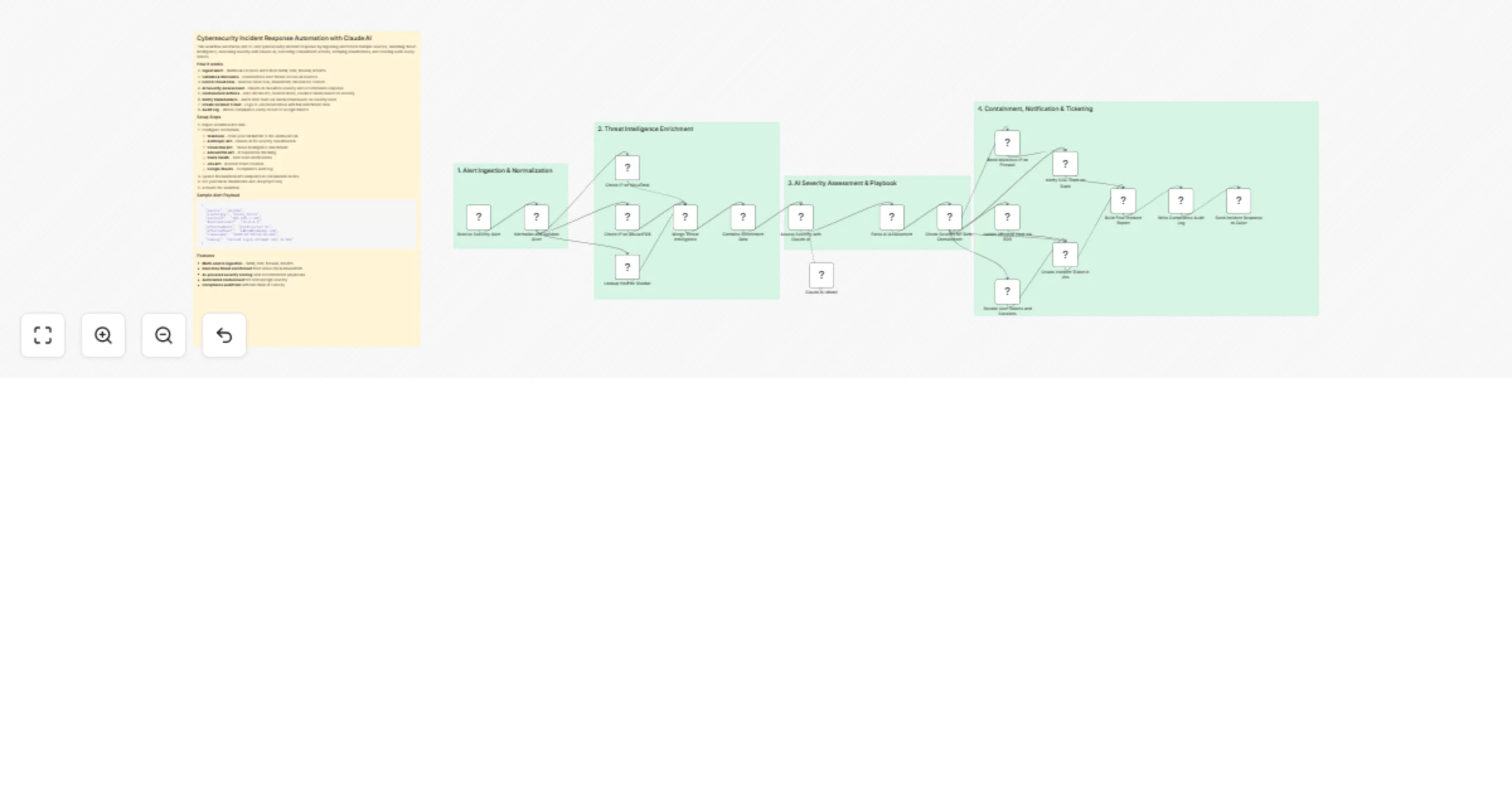
Workflow preview

$20/month : Unlimited workflows
2500 executions/month

THE #1 IN WEB SCRAPING
Scrape any website without limits
HOSTINGER  Early Deal
Early Deal
DISCOUNT 20% Try free
 Early Deal
Early DealDISCOUNT 20%
Self-hosted n8n
Unlimited workflows - from $4.99/mo

#1 hub for scraping, AI & automation
6000+ actors - $5 credits/mo
Overview
This workflow automates end-to-end cybersecurity incident response by ingesting alerts from multiple sources, enriching threat intelligence, assessing severity with Claude AI, executing containment actions, notifying stakeholders, and creating audit-ready tickets.
How it works
- Ingest Alert - Webhook receives alerts from SIEM, EDR, firewall, IDS/IPS
- Validate & Normalize - Standardizes alert format across all sources
- Enrich Threat Intel - Queries VirusTotal, AbuseIPDB, Shodan for context
- AI Severity Assessment - Claude AI classifies severity and recommends response
- Containment Actions - Auto-blocks IPs, isolates hosts, revokes tokens based on severity
- Notify Stakeholders - Alerts SOC team via Slack/email based on severity level
- Create Incident Ticket - Logs to Jira/ServiceNow with full enrichment data
- Audit Log - Writes compliance-ready record to Google Sheets
Setup Steps
- Import workflow into n8n
- Configure credentials:
- Webhook - Point your SIEM/EDR to the webhook URL
- Anthropic API - Claude AI for severity classification
- VirusTotal API - Threat intelligence enrichment
- AbuseIPDB API - IP reputation checking
- Slack OAuth - SOC team notifications
- Jira API - Incident ticket creation
- Google Sheets - Compliance audit log
- Update firewall/EDR API endpoints in containment nodes
- Set your Slack channel IDs and Jira project key
- Activate the workflow
Sample Alert Payload
{
"source": "splunk",
"alertType": "brute_force",
"sourceIP": "192.168.1.100",
"destinationIP": "10.0.0.5",
"affectedHost": "prod-server-01",
"affectedUser": "[email protected]",
"timestamp": "2025-02-22T10:30:00Z",
"rawLog": "Failed login attempt x50 in 60s"
}
Features
- Multi-source ingestion - SIEM, EDR, firewall, IDS/IPS
- Real-time threat enrichment from VirusTotal & AbuseIPDB
- AI-powered severity scoring with recommended playbooks
- Automated containment for Critical/High severity
- Compliance audit trail with full chain of custody
Industries That Benefit
- Financial Services: Rapid containment of fraud and data exfiltration attempts.
- Healthcare: Protect PHI with automated isolation and HIPAA-compliant logging.
- Retail & E-commerce: Prevent POS breaches and payment card compromises.
- Government & Defense: Enforce zero-trust response with full audit trails.
- Critical Infrastructure: Contain OT threats before operational disruption.
Prerequisites
- SIEM/EDR alerting configured to forward to webhook
- API access to threat intelligence platforms (VirusTotal, OTX, MISP)
- EDR (CrowdStrike, Carbon Black) or firewall API credentials
- ITSM system (Jira, ServiceNow) with API access
- n8n instance with HTTP Request, Function, Slack, and Email nodes enabled
- SMTP, Slack, or SMS gateway credentials
Modification Options
- Add phishing triage with email detonation sandbox.
- Integrate SOAR playbooks for ransomware response.
- Enable auto-remediation (e.g., disable user in AD).
- Add forensic artifact collection (memory dump, logs).
- Trigger war room creation in Slack/Teams for Major incidents.
- Export incidents to case management (e.g., TheHive, Cortex).
Explore More Cybersecurity Automation Workflows: Contact us to build custom SOAR, threat hunting, and compliance automation solutions powered by n8n and AI.