Secure user emails with AES-256 encryption and verification system
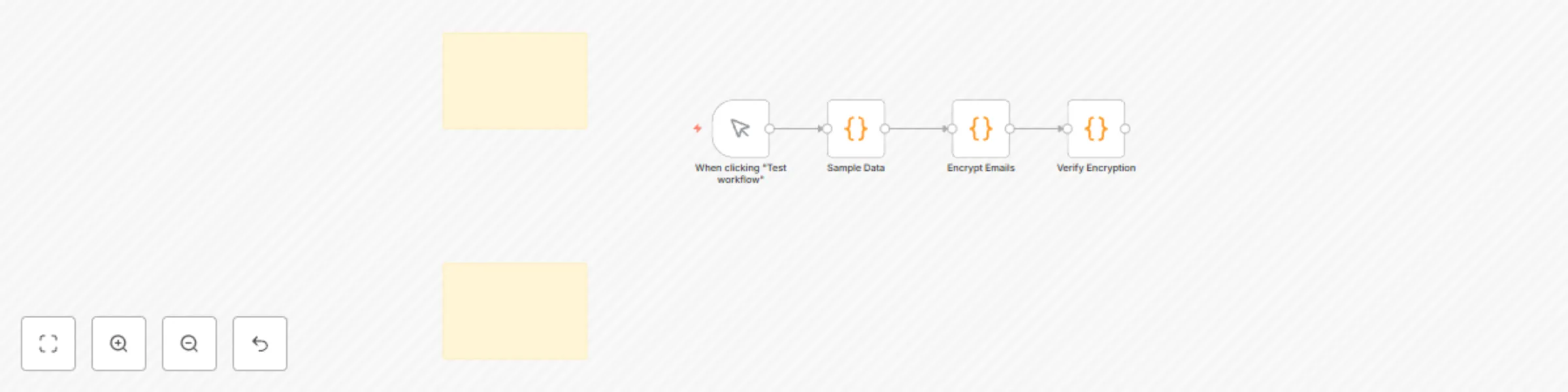
Workflow preview


 Early Deal
Early DealDISCOUNT 20%

Important notice
This workflow is provided as-is. Please review and test before using in production.
Overview
🔐 Email Encryption Masterclass
Professional-Grade AES-256 Data Protection for n8n
How It Works
This comprehensive workflow demonstrates enterprise-level email encryption using industry-standard AES-256-CBC encryption. Perfect for organizations handling sensitive customer data who need to comply with GDPR, HIPAA, or other data protection regulations.
The workflow processes data in three secure stages:
- Sample Data Generation - Creates test user records with emails for demonstration
- Email Encryption - Applies AES-256-CBC encryption with unique initialization vectors (IVs) for each record
- Verification System - Decrypts and validates the encrypted data to ensure integrity
Each email address is encrypted with a randomly generated IV, making every encryption unique even for identical email addresses. The system includes comprehensive error handling and provides detailed processing status for audit trails.
Key Features
✅ Military-Grade Security: AES-256-CBC encryption with unique IVs
✅ Compliance Ready: Built for GDPR, HIPAA, and SOX requirements
✅ Batch Processing: Handles large datasets efficiently
✅ Error Handling: Graceful failure management with detailed logging
✅ Verification System: Built-in decryption validation
✅ Audit Trail: Complete processing timestamps and status tracking
✅ Production Ready: Includes security best practices and key management guidance
Setup Steps
1. Import the Workflow
- Download the JSON file
- In n8n, go to Workflows → Import from File
- Select the downloaded JSON file
- Click Import
2. Configure Security Settings
- Open the Encrypt Emails node
- Replace the default secret key with your own 32-character secure key:
const secret = 'your_32_character_secret_key_here!'; - Important: In production, use environment variables for the secret key
3. Set Up Sample Data (Optional)
- The workflow includes sample user data for testing
- Replace with your actual data source (database, API, CSV, etc.)
- Ensure your data has an
emailfield
4. Test the Workflow
- Click Execute workflow to run the complete process
- Review the encrypted results in each node
- Verify that emails are properly encrypted and can be decrypted
5. Production Deployment
- Remove the
originalEmailfield from output (line 45 in Encrypt Emails node) - Store your secret key in environment variables
- Set up proper key rotation schedule
- Configure monitoring and alerting for failed encryptions
Security Best Practices Included
🔒 Unique IVs: Every encryption uses a fresh random initialization vector 🔒 Proper Key Length: Enforces 32-byte keys for AES-256 🔒 Error Isolation: Failed encryptions don't break the entire batch 🔒 No Key Exposure: Secret keys are never logged or stored in output 🔒 Verification Loop: Ensures encrypted data can be successfully decrypted
Use Cases
- Customer Data Protection: Encrypt email addresses in CRM systems
- Compliance Requirements: Meet GDPR, HIPAA, SOX data protection mandates
- Data Warehouse Security: Protect PII in analytics databases
- Secure Data Transfer: Encrypt sensitive data before API transmission
- Audit Preparation: Demonstrate proper data protection controls
This workflow represents years of cybersecurity expertise condensed into a ready-to-use automation solution. Perfect for developers, security professionals, and compliance teams who need reliable data encryption.