Gate deployments on WAF scan results with WAFtester
Workflow preview

$20/month : Unlimited workflows
2500 executions/month

THE #1 IN WEB SCRAPING
Scrape any website without limits
HOSTINGER  Early Deal
Early Deal
DISCOUNT 20% Try free
 Early Deal
Early DealDISCOUNT 20%
Self-hosted n8n
Unlimited workflows - from $4.99/mo

#1 hub for scraping, AI & automation
6000+ actors - $5 credits/mo
Overview
What it does
A CI/CD quality gate that blocks deployments when WAF protection is insufficient. Your pipeline sends a webhook with the target URL, the workflow runs WAFtester scans, and returns a pass/fail HTTP response the pipeline can gate on.
About WAFtester
WAFtester is an open-source CLI for testing Web Application Firewalls. It ships 27 MCP tools, 2,800+ attack payloads across 18 categories (SQLi, XSS, SSRF, SSTI, command injection, XXE, and more), detection signatures for 26 WAF vendors and 9 CDNs, and enterprise-grade assessment with F1/MCC scoring and letter grades (A+ through F).
- GitHub: github.com/waftester/waftester
- Docs: Installation | Examples | Commands
Who it's for
- DevOps teams enforcing security gates in CI/CD
- Platform engineers automating deployment approvals
- Security teams requiring pre-deploy WAF validation
How it works
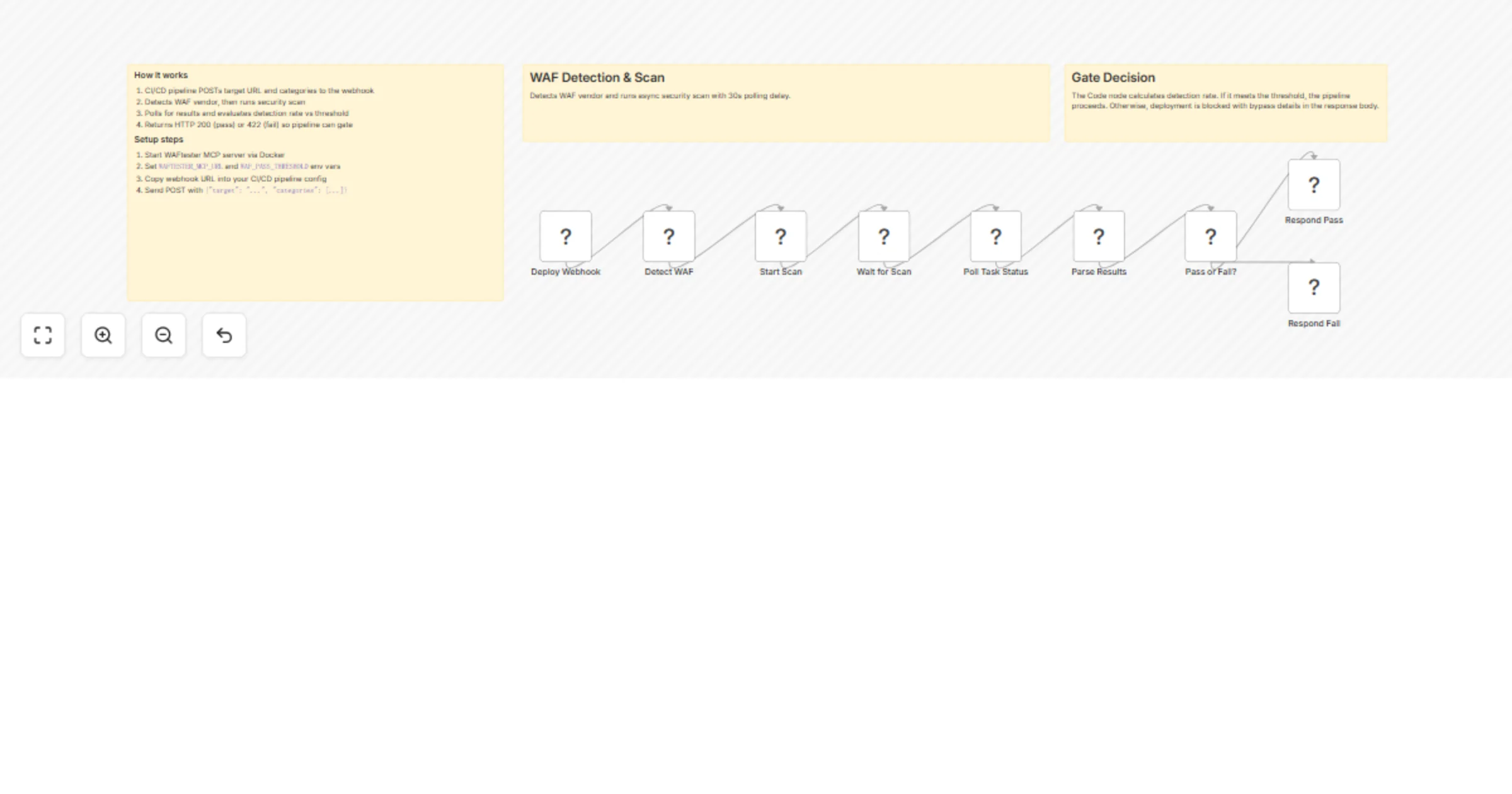
The workflow has seven nodes:
- Webhook — Receives a POST with
{"target": "https://staging.example.com", "categories": ["sqli", "xss"]} - Detect WAF — Calls WAFtester's
detect_waftool to fingerprint the WAF vendor - Start Scan — Launches an async
scantask with the requested attack categories - Wait — Pauses to let the scan run
- Poll Results — Calls
get_task_statusto retrieve completed results - Evaluate — Compares the detection rate against
WAF_PASS_THRESHOLD - Respond — Returns HTTP 200 (pass, deploy allowed) or HTTP 422 (fail, deploy blocked) with bypass details
CI/CD integration example
# In your pipeline
RESPONSE=$(curl -s -w "%{http_code}" -o body.json \
-X POST https://your-n8n/webhook/waf-gate \
-H "Content-Type: application/json" \
-d '{"target": "https://staging.example.com", "categories": ["sqli", "xss"]}')
if [ "$RESPONSE" != "200" ]; then echo "WAF gate failed"; exit 1; fi