R
Rajneesh Gupta
2
Workflows
Workflows by Rajneesh Gupta
Free advanced
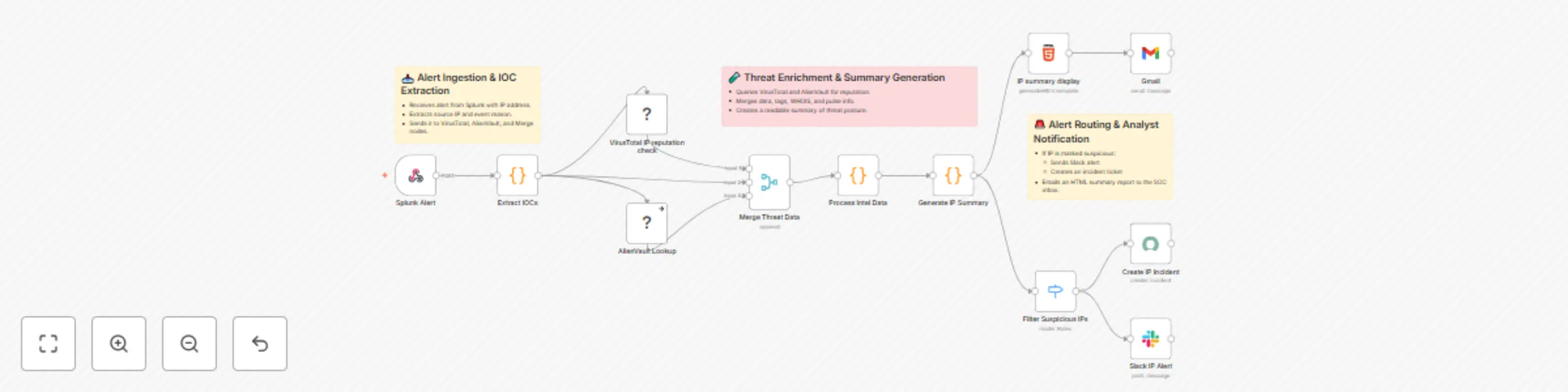
IP reputation check & SOC alerts with Splunk, VirusTotal and AlienVault
IP Reputation Check & Threat Summary using Splunk + VirusTotal + AlienVault + n8n This workflow automates IP reputati...
R
Rajneesh Gupta SecOps
16 Jul 2025
1652
0
Free intermediate
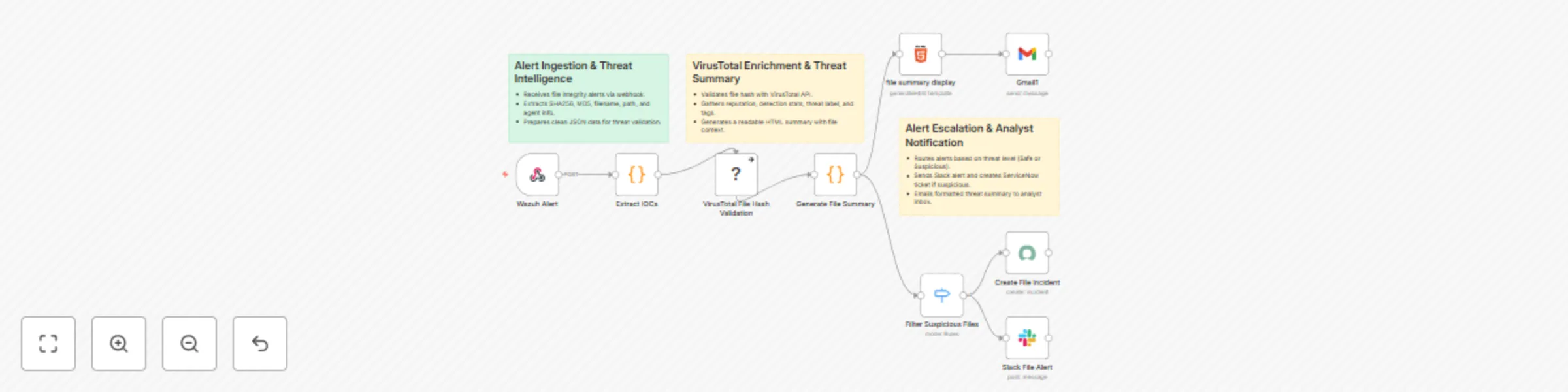
Malicious file detection & response: Wazuh to VirusTotal with Slack alerts
Malicious File Detection & Threat Summary Automation using Wazuh + VirusTotal + n8n This workflow helps SOC teams aut...
R
Rajneesh Gupta SecOps
14 Jul 2025
2085
0