Sean Birmingham
Workflows by Sean Birmingham
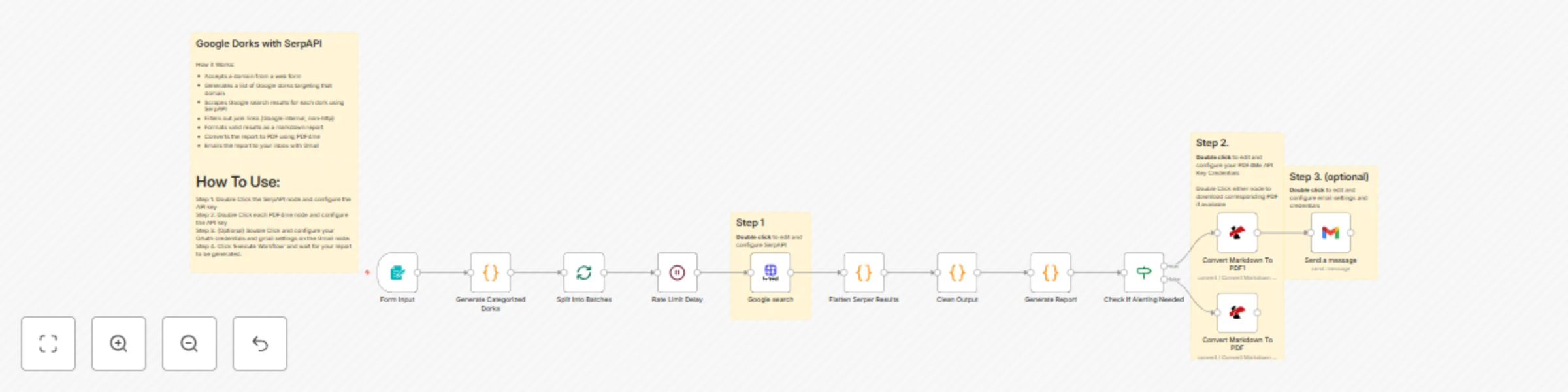
Generate security vulnerability reports with Google Dorks, SerpAPI and PDF4me
Google Dorks with SerpAPI How it Works: Accepts a domain from a web form Generates a list of Google dorks targeting t...
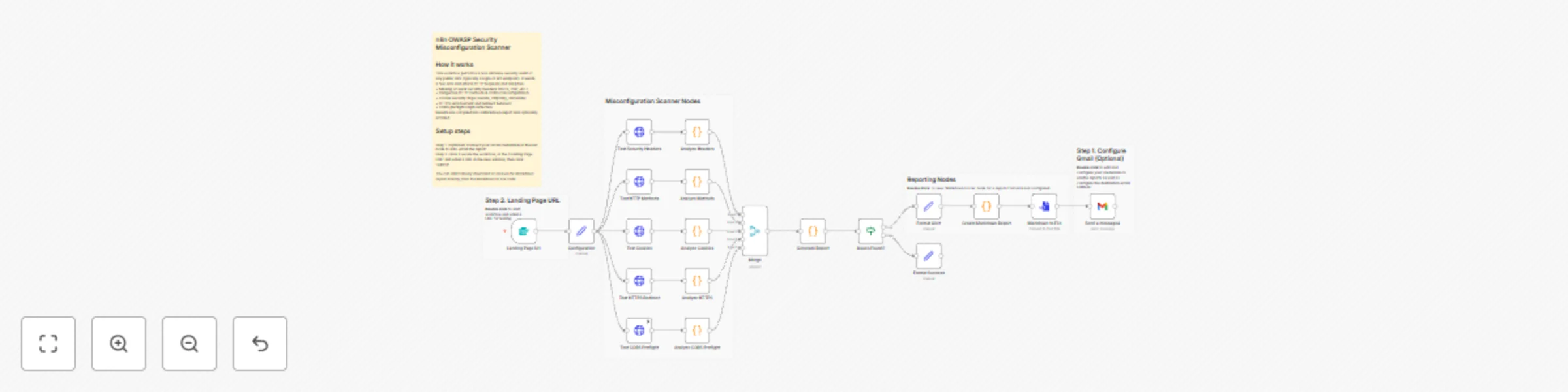
Web security scanner for OWASP compliance with Markdown reports
How the n8n OWASP Scanner Works & How to Set It Up How It Works (Simple Flow): 1. Input : Enter target URL + endpoint...
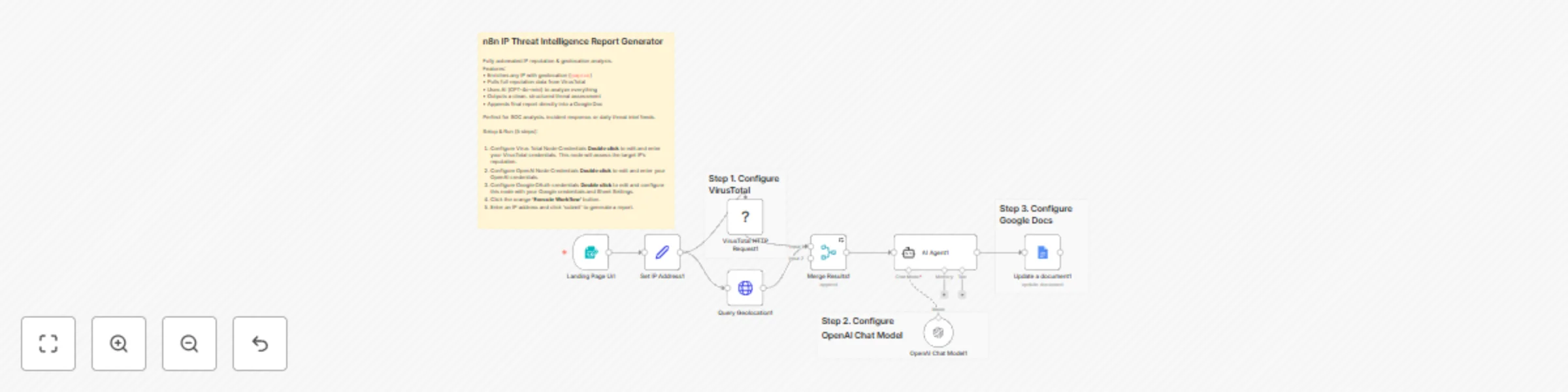
IP threat intelligence report generator with VirusTotal, OpenAI and Google Docs
Cybersec IP Intelligence Gatherer This project utilizes the VirusTotal node and Geolocation node to thoroughly gather...
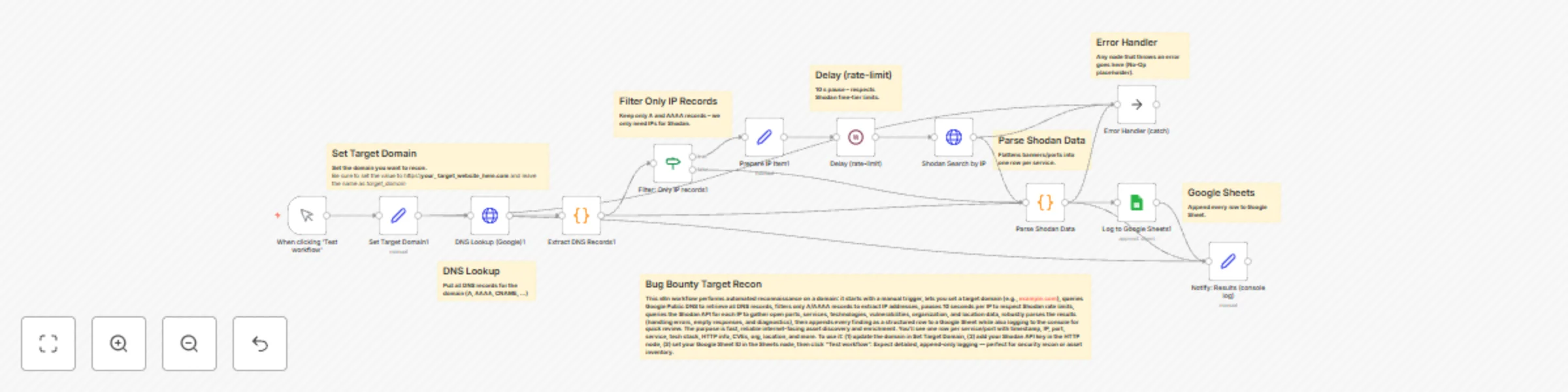
Automate external attack surface mapping with Shodan API and DNS lookups
The Bug Bounty Target Recon n8n workflow is a powerful automation tool for security professionals and ethical hackers...

Security reconnaissance with Google Dorks, Parsera scraping, and Gmail reports
This workflow contains community nodes that are only compatible with the self hosted version of n8n. How it Works: 1....

JavaScriptSentry: detect sensitive information in JavaScript
This workflow contains community nodes that are only compatible with the self hosted version of n8n. How It works: Wh...
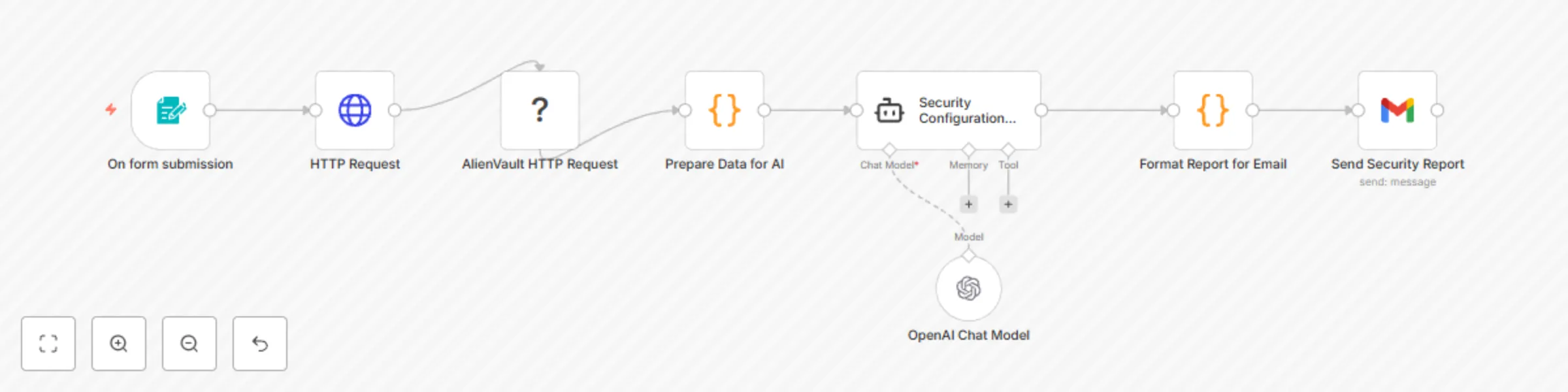
OTX & OpenAI web security check
This n8n workflow automates website security audits. It combines direct website scanning, threat intelligence from Al...