Tenkay
Workflows by Tenkay

Compare lists and identify common items & differences using custom keys
This workflow compares two lists of objects (List A and List B) using a user-specified key (e.g. `email`, `id`, `domain`) and returns: - Items common to both lists (based on the key) - Items only in List A - Items only in List B ### How it works: 1. Accepts a JSON input containing: - `listA`: the first list of items - `listB`: the second list of items - `key`: the field name to use for comparison 2. Performs a field-based comparison using the specified key 3. Returns a structured output: - `common`: items with matching keys (only one version retained) - `onlyInA`: items found only in List A - `onlyInB`: items found only in List B ### Example Input: ```json { "key": "email", "listA": [ { "email": "[email protected]", "name": "Alice" }, { "email": "[email protected]", "name": "Bob" } ], "listB": [ { "email": "[email protected]", "name": "Bobby" }, { "email": "[email protected]", "name": "Carol" } ] } ``` ### Output: - `common`: `[ { "email": "[email protected]", "name": "Bob" } ]` - `onlyInA`: `[ { "email": "[email protected]", "name": "Alice" } ]` - `onlyInB`: `[ { "email": "[email protected]", "name": "Carol" } ]` ### Use Cases: - Deduplicate data between two sources - Find overlapping records - Identify new or missing entries across systems This workflow is useful for internal data auditing, list reconciliation, transaction reconciliation, or pre-processing sync jobs.
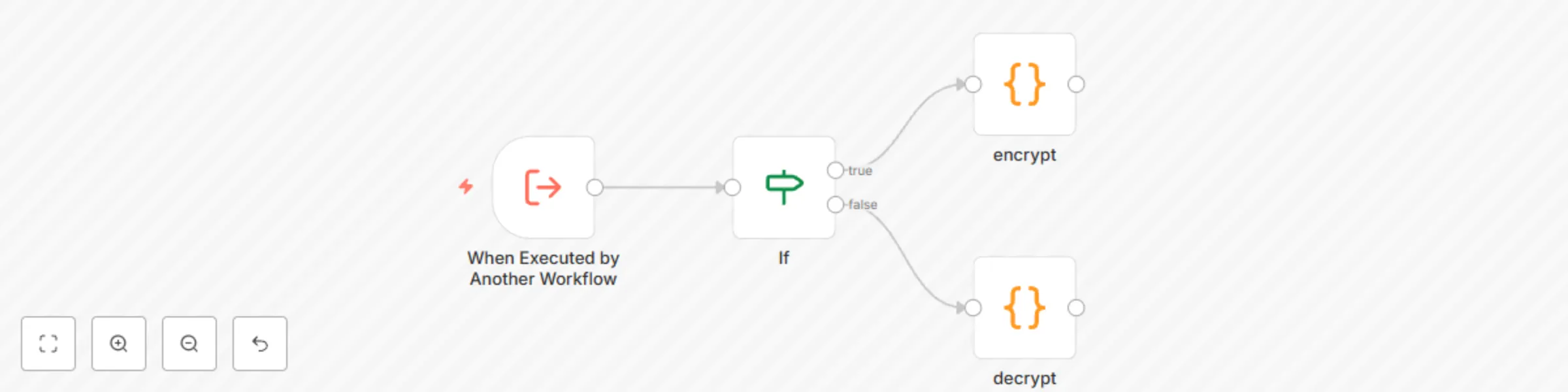
XOR encryption and decryption with Base64 encoding for workflow data
This workflow performs basic XOR-based encryption and decryption using a custom password. It is intended to be triggered by another workflow and processes structured input in JSON format. ### Input Structure The workflow expects a single array of objects with the following fields: - `action-type`: either `"encrypt"` or `"decrypt"` - `key`: the password used for encryption and decryption - `data`: the content to encrypt or decrypt ### Example: Encryption Input ```json [ { "action-type": "encrypt", "key": "Password", "data": "Hello, this is a secret message" } ] ``` ### Example: Decryption Input ```json [ { "action-type": "decrypt", "key": "Password", "data": "ChwGAQceF15eE2QXFRcUagxGVgV8TBoNBA4VQVoQZkwVUhImU1FTEg==" } ] ``` ### Output The output returns an array of results, each containing either the encrypted string (base64 format) or the decrypted plain text. ### Use Case This workflow is useful for simple internal message encoding, data obfuscation, or testing purposes. It is not recommended for securing sensitive or personal data, as XOR encryption is not cryptographically secure. The workflow logic is written in JavaScript using n8n Function nodes, without any external dependencies.