Javier Rieiro
Workflows by Javier Rieiro
Scan single URLs for security vulnerabilities with GPT-4 (JS, PHP, Python)
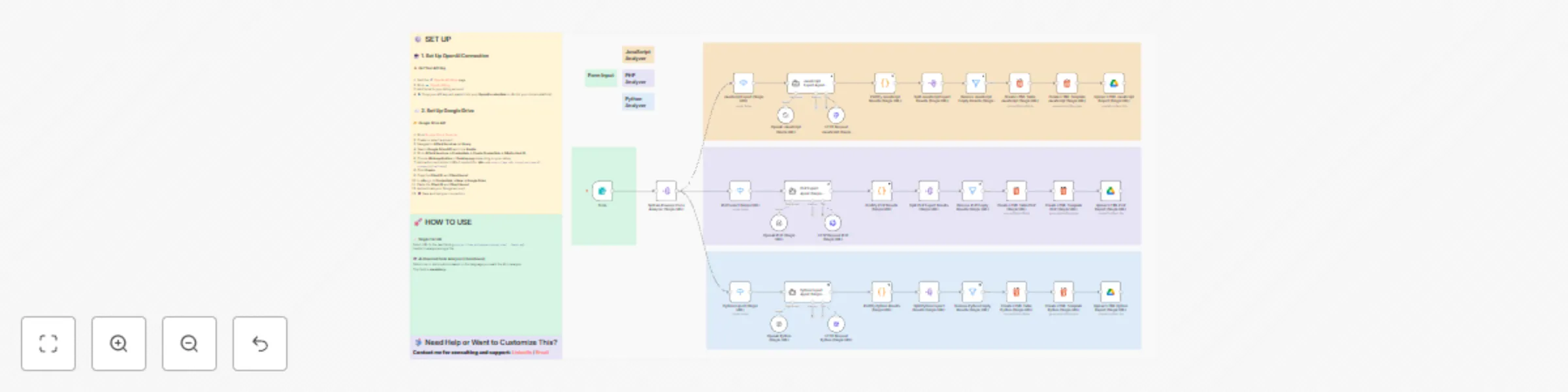
## Overview This **workflow** automates static security analysis for **JavaScript, PHP, and Python** codebases. It’s designed for **bug bounty hunters** and **security researchers** who need fast, structured, and AI-assisted vulnerability detection across multiple sources. --- ## Features - 🤖 **AI-Powered Analysis**: - Specialized agents for each language: - **AI JavaScript Expert** - **AI PHP Expert** - **AI Python Expert** - Each agent detects **only exploitable vulnerabilities** (AST + regex heuristics). - Returns strict JSON with: ```json { "results": [ { "url": "file or URL", "code": "lines + snippet", "severity": "medium|high|critical", "vuln": "vulnerability type" } ] } ``` - 🧩 **Post-Processing**: - Cleans, formats, and validates JSON results. - Generates **HTML tables** with clear styling for quick visualization. --- ## Output - ✅ JSON vulnerability reports per file. - 📊 HTML table summaries grouped by language and severity. --- ## Usage 1. Import the workflow into **n8n**. 2. Configure credentials: - OpenAI API key - GitHub API Key - Google Drive API Key 3. Run via the provided **webhook form**. 4. Select analysis mode and input target. 5. View structured vulnerability reports directly in n8n or Google Drive. --- ## Notes - Performs **static analysis only** (no code execution). - Detects **exploitable findings only**; ignores low-impact issues. ---
Automate CVE detection with AI-powered Nuclei template generation & Google Drive
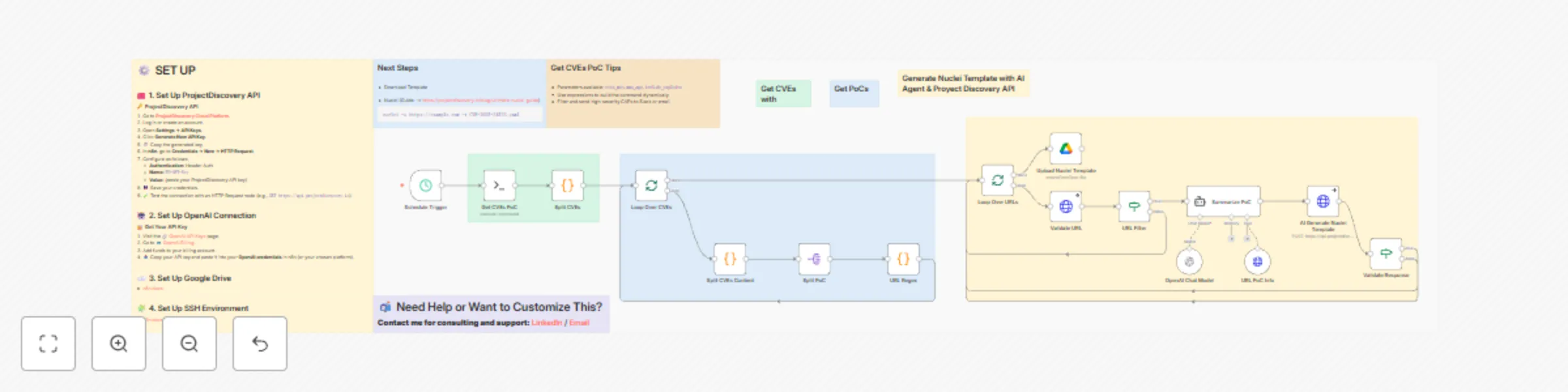
## Short description Automates collection, technical extraction, and automatic generation of Nuclei templates from public CVE PoCs. Converts verified PoCs into reproducible detection templates ready for testing and distribution. ## Purpose Provide a reliable pipeline that turns public proof-of-concept data into usable detection artifacts. Reduce manual work involved in finding PoCs, extracting exploit details, validating sources, and building Nuclei templates. ## How it works (technical summary) 1. Runs a scheduled SSH job that executes `vulnx` with filters for recent, high-severity PoCs. 2. Parses the raw `vulnx` output and splits it into individual CVE entries. 3. Extracts structured fields: CVE ID, severity, title, summary, risk, remediation, affected products, POCs, and references. 4. Extracts URLs from PoC sections using regex. 5. Validates each URL with HTTP requests. Invalid or unreachable links are logged and skipped. 6. Uses an AI agent (OpenAI via LangChain) to extract technical artifacts: exploit steps, payloads, endpoints, raw HTTP requests/responses, parameters, and reproduction notes. The prompt forces technical-only output. 7. Sends the extracted technical content to ProjectDiscovery Cloud API to generate Nuclei templates. 8. Validates AI and API responses. Accepted templates are saved to a configured Google Drive folder. 9. Produces JSON records and logs for each processed CVE and URL. ## Output - Nuclei templates in ProjectDiscovery format (YAML) stored in Google Drive. - Structured JSON per CVE with metadata and extracted technical details. - Validation logs for URL checks, AI extraction, and template generation. ## Intended audience - Bug bounty hunters. - Security researchers and threat intel teams. - Automation engineers who need reproducible detection templates. ## Setup & requirements - n8n instance with workflow imported. - SSH access to a host with `vulnx` installed. - OpenAI API key for technical extraction. - ProjectDiscovery API key for template generation. - Google Drive OAuth2 credentials for storing templates. - Configure schedule trigger and target Google Drive folder ID. ## Security and usage notes - Performs static extraction and validation only. No active exploitation. - Processes only PoCs that meet configured filters (e.g., CVSS > 6). - Use responsibly. Do not target systems you do not own or have explicit permission to test.
Automated CVE scanning of Bug Bounty programs with Nuclei and Project Discovery
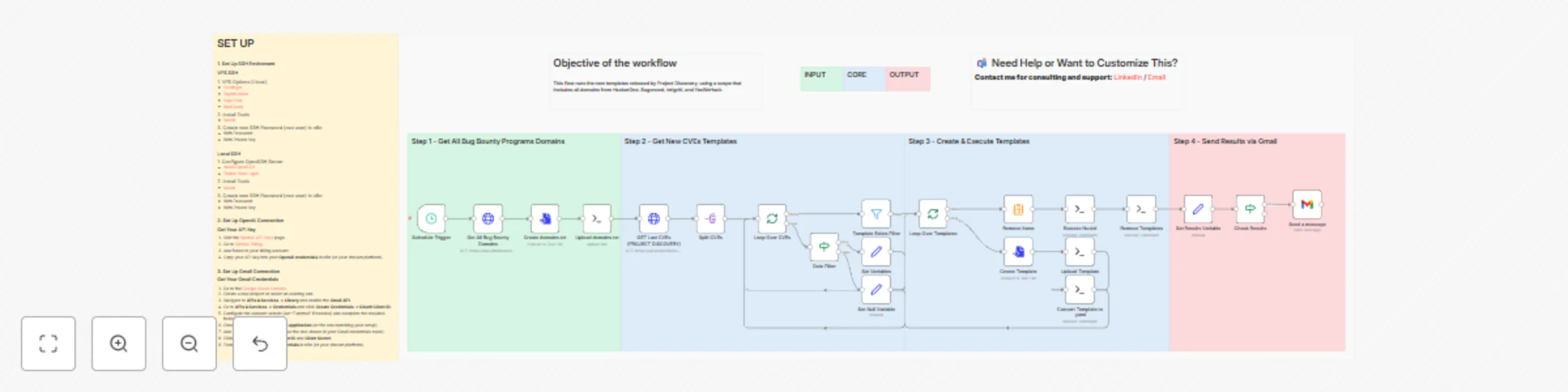
## Description Automates daily CVE-driven scanning against bug bounty scopes. It fetches bug-bounty domains, pulls newly published Project Discovery templates, converts them to Nuclei rules, runs targeted scans, and emails findings. ## Objective Help security researchers and bug bounty hunters discover exploitable instances quickly by automatically running the latest public templates from Project Discovery against a consolidated bug-bounty scope. Reduce manual steps and maintain continuous reconnaissance. ## How it works 1. The workflow accepts or fetches a domain list that covers HackerOne, Bugcrowd, Intigriti, and YesWeHack. 2. It downloads the latest public templates from Project Discovery. 3. For each new template published since the last run it: creates a file, uploads it to a remote host, and converts it to a Nuclei-compatible YAML. 4. It uploads a consolidated domains wordlist to the remote host. 5. It executes Nuclei with the new templates against the domains list using configured flags (concurrency, rate limits, severity tags). 6. It collects and deduplicates Nuclei output. 7. If results exist, it sends the findings via Gmail. ## Requirements • SSH access (root or equivalent) to a VPS or host. • Nuclei installed on the remote host. • Gmail OAuth2 credentials for sending notifications. • Recommended: VPS with enough CPU and network capacity for concurrent scanning when scope is large.

Subdomain enumeration with Subfinder, HTTPX & GPT-4-Mini for security reconnaissance
Generates a wordlist of 1,000–15,000 subdomains created by an AI agent by correlating detected technologies and recurring patterns. ## **Objective** Assist security researchers, bug bounty hunters, and web pentesters in the reconnaissance phase by incorporating an AI agent that generates additional potential subdomains. This enables discovery of assets outside the scope of traditional scans and expands the analyzable attack surface. ## **How it works** 1. The user uploads a list of domains to scan (scope). 2. The workflow performs a passive, comprehensive scan using four sources (subfinder, assetfinder, crt.sh, Wayback Machine). 3. The scan results and detected technologies are passed to an AI agent. 4. The agent runs in a loop up to 20 iterations, generating new subdomains each pass (average output depends on input and model). 5. Generated subdomains are validated and deduplicated. Syntax is checked and availability is tested (host active / httpx). ### Requirements - SSH access with a root user and the following tools: 1. [Subfinder](https://github.com/projectdiscovery/subfinder) 2. [Assetfinder](https://github.com/tomnomnom/assetfinder) 3. [HTTPX](https://github.com/projectdiscovery/httpx) It is recommended to use a VPS with SSH because if the scope is very large the workflow will take a long time.