K
Kunsh
3
Workflows
Workflows by Kunsh

Free intermediate
Monitor new CVEs for bug bounty hunting with Gemini AI and Slack alerts
How it works Automatically monitors NIST's CVE database every hour for new vulnerabilities and uses AI to assess thei...
K
Kunsh SecOps
5 Sep 2025
851
0
Free intermediate
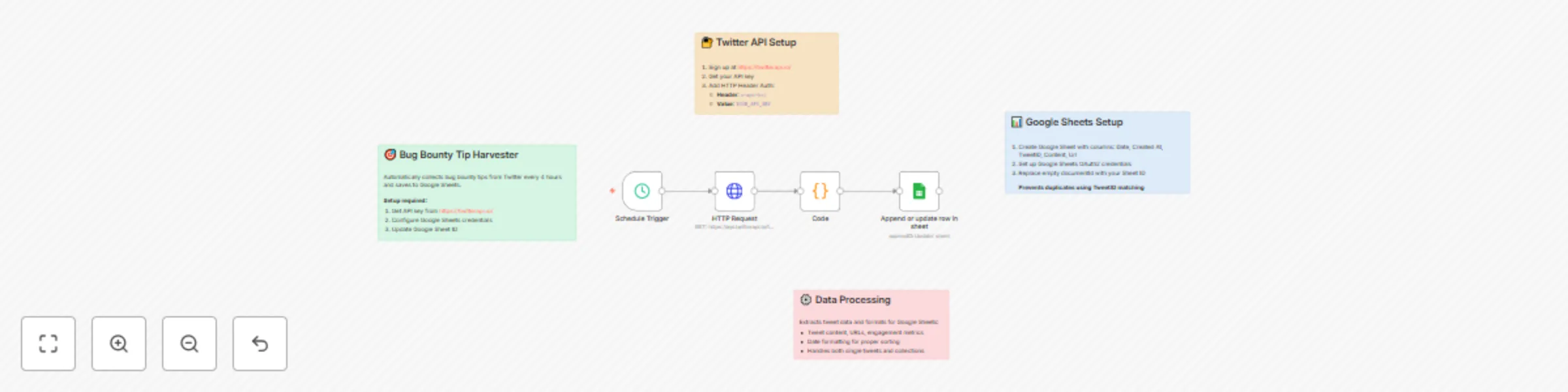
Automatically collect bug bounty tips from Twitter to Google Sheets
How it works Automatically monitors Twitter for bug bounty tips and educational content every 4 hours, then saves val...
K
Kunsh Market Research
2 Sep 2025
290
0
Free intermediate
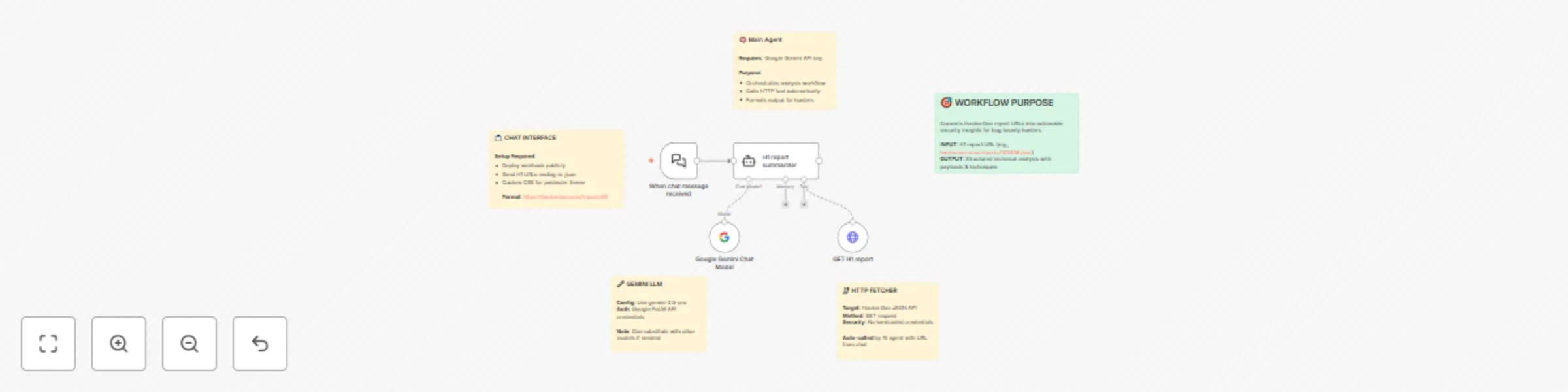
Extract actionable security insights from HackerOne reports with Google Gemini
A streamlined AI powered tool that extracts actionable technical insights from HackerOne security reports for advance...
K
Kunsh SecOps
23 Jul 2025
605
0