Yehor EGMS
4
Workflows
Workflows by Yehor EGMS
Free advanced
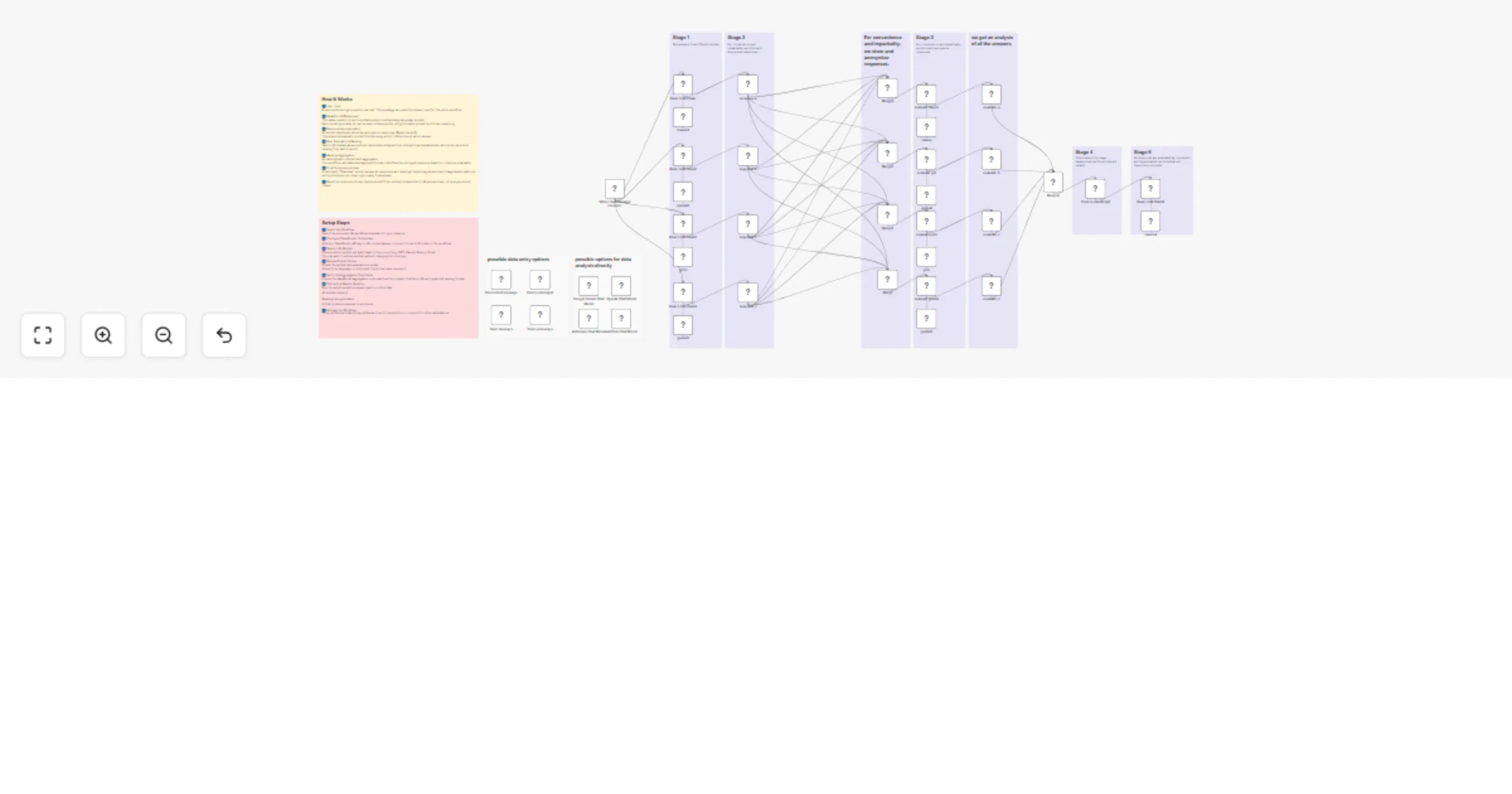
Generate consensus-based answers using Claude, GPT, Grok and Gemini
The original LLM Council concept was introduced by Andrej Karpathy and published as an open source repository demonst...
Engineering
5 Jan 2026
413
0
Free advanced
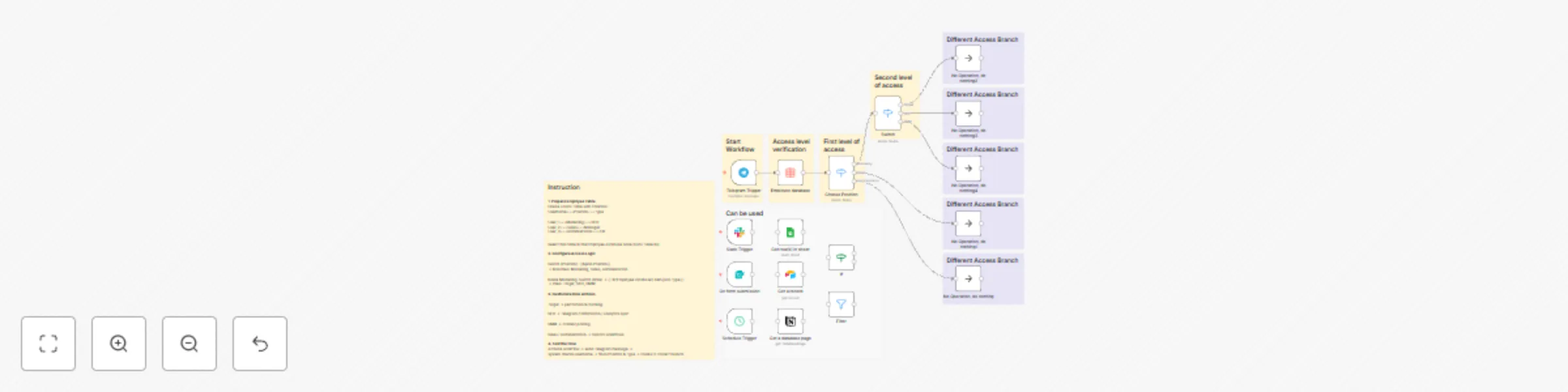
Role-based access control (RBAC) for Telegram automations
🔐 n8n Workflow: Role Based Access Control (RBAC) for Telegram Automations This n8n workflow lets you control access...
Miscellaneous
25 Oct 2025
127
0
Free advanced
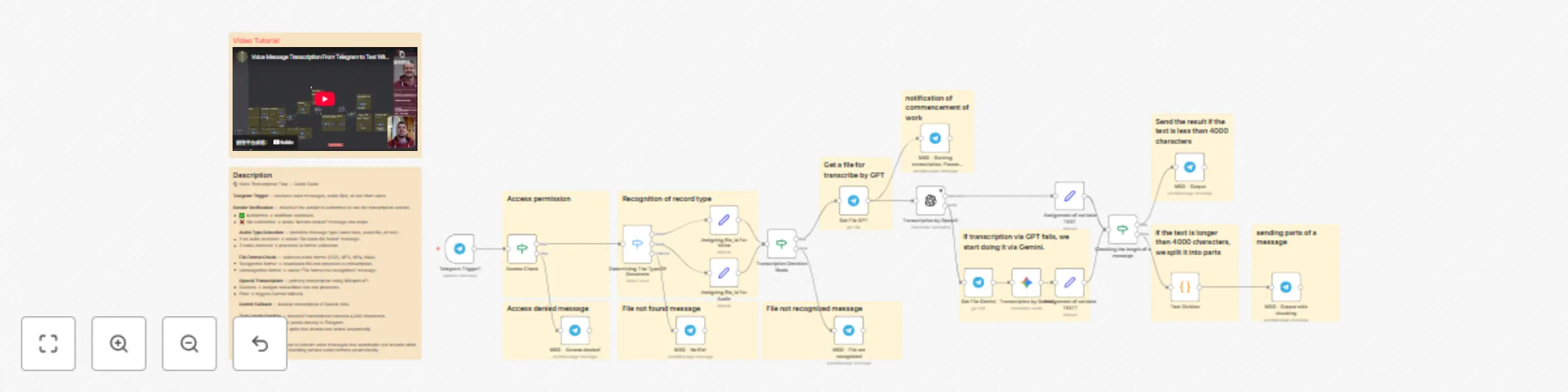
Transcribing Telegram voice messages using Whisper and Gemini with a fallback mechanism
🎙️ n8n Workflow: Voice Message Transcription with Access Control This n8n workflow enables automated transcription o...
Document Extraction
14 Oct 2025
267
0

Free advanced
Telegram chat access control with user permission database
🔐 n8n Workflow: Access Control for Internal Chats or Chatbots This n8n workflow helps you restrict access to your in...
Miscellaneous
14 Oct 2025
109
0