Adnan Tariq
Workflows by Adnan Tariq
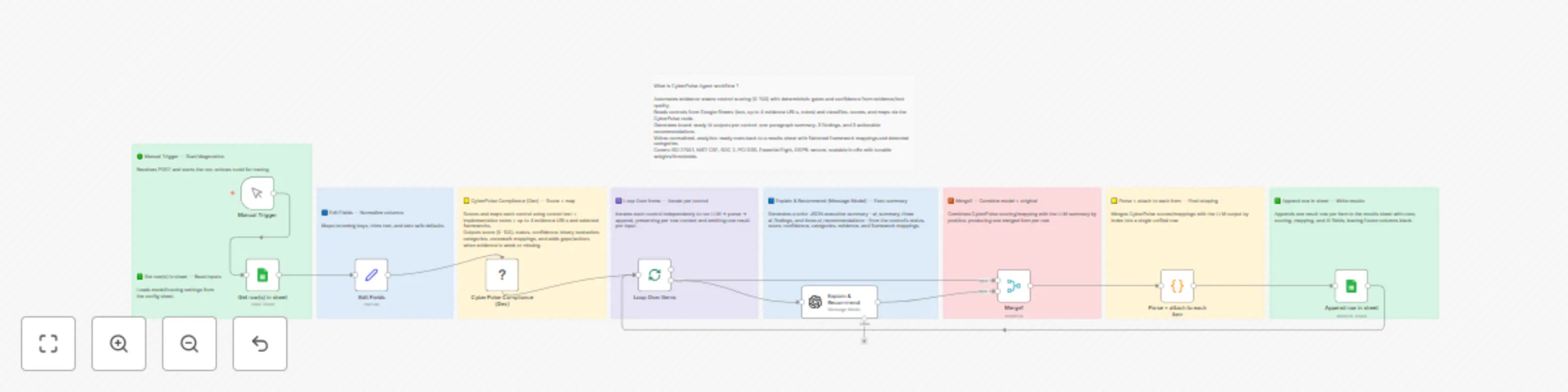
Automated compliance control scoring with CyberPulse, GPT-4o & Google Sheets
What this template does Batch evaluates compliance controls from Google Sheets using the CyberPulse Compliance API. E...
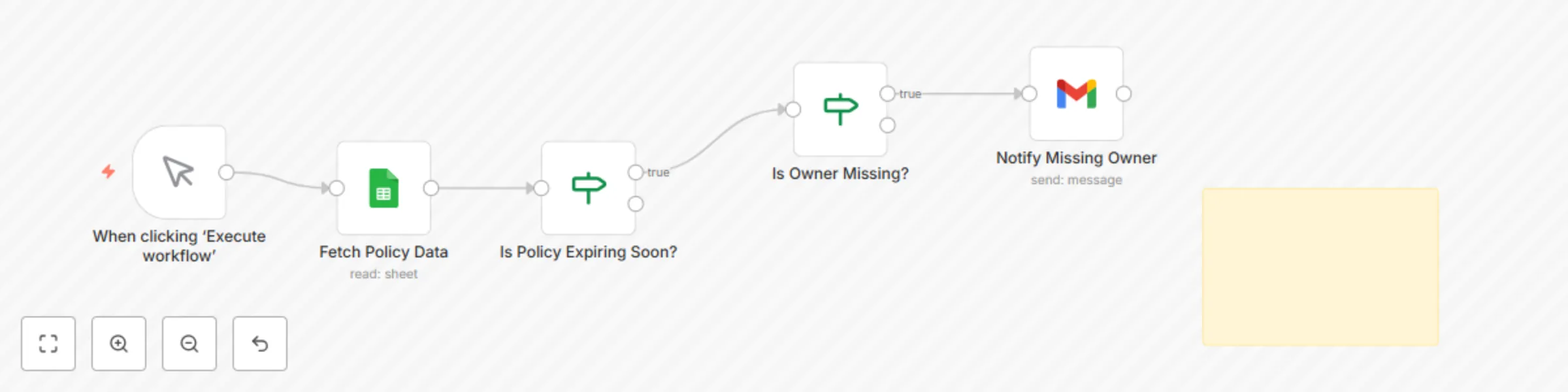
Track policy expiry dates and ownership with Google Sheets and Gmail notifications
Purpose Automates the monitoring of policy documents for expiry and ownership gaps. Ensures accountability by sending...
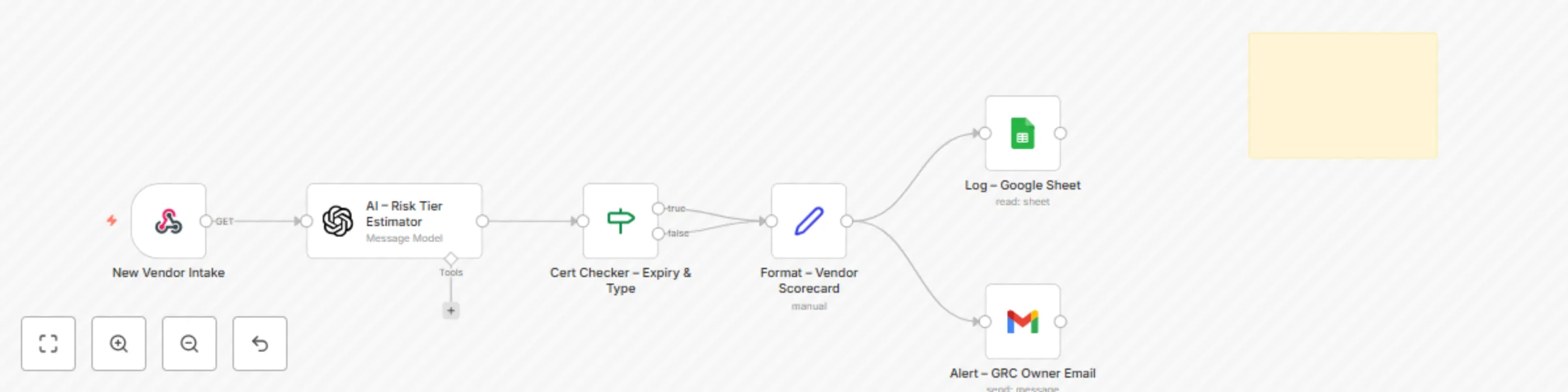
CYBERPULSE AI GRC: Vendor risk evaluator
Description Automates the intake, classification, and documentation of third party vendors. Evaluates vendor function...

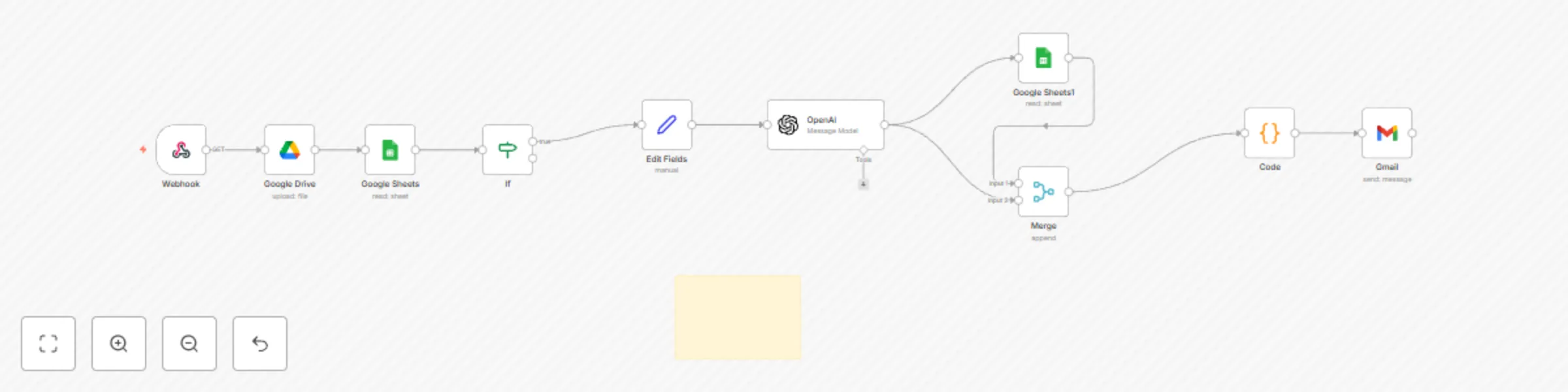
Automate risk treatment tasks with Google Sheets for GRC compliance
Description Automatically assigns and escalates risk treatment tasks based on severity, organizational unit, and asse...
Cyberpulse AI GRC: Automate security questionnaire responses
Description Automates vendor/customer security questionnaire responses. It ingests a questionnaire (Sheet/CSV/XLSX),...
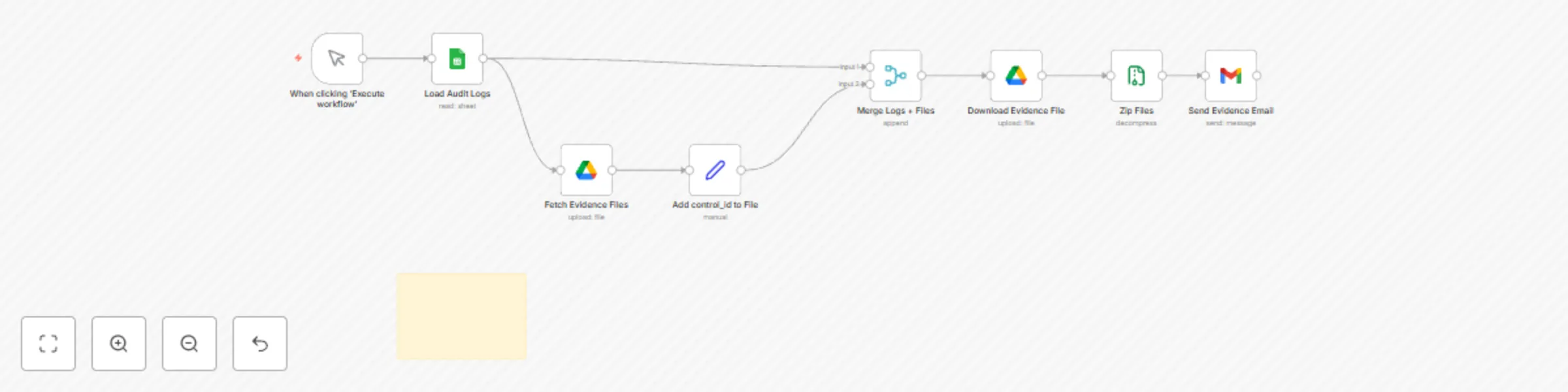
CYBERPULSE AI GRC: automate compliance audit documentation
Description Automatically packages audit ready evidence files matched to control IDs from ISO 42001 or other framewor...

CYBERPULSE AI GRC: automated ISO 42001 compliance evaluation
Description Automatically evaluates and maps AI governance responses to ISO 42001:2023 clause requirements using AI p...
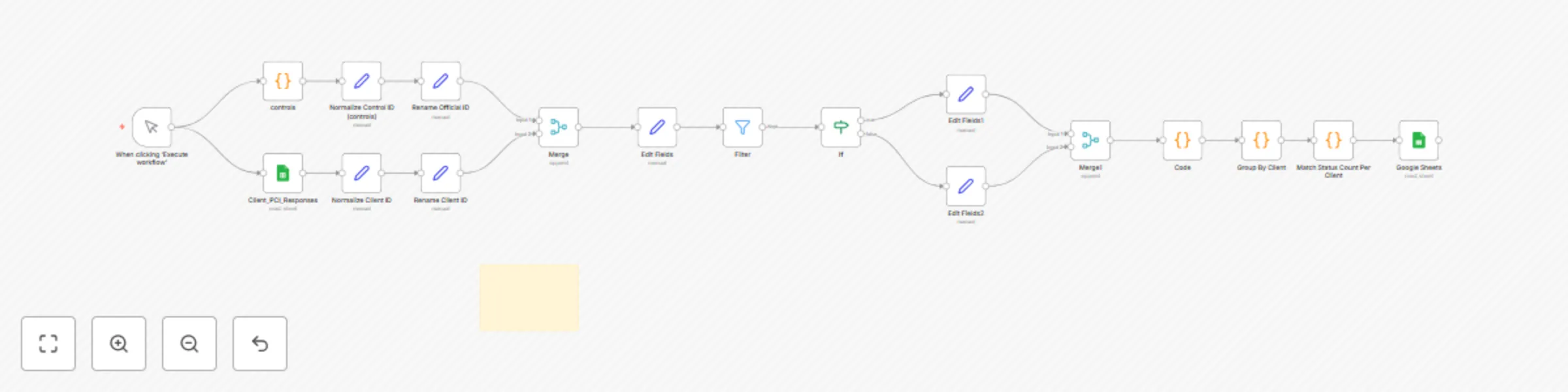
CYBERPULSE AI GRC: automate PCI DSS control evaluation and compliance tracking
Description Automatically evaluates PCI DSS control responses using logic or AI. Designed to speed up compliance work...
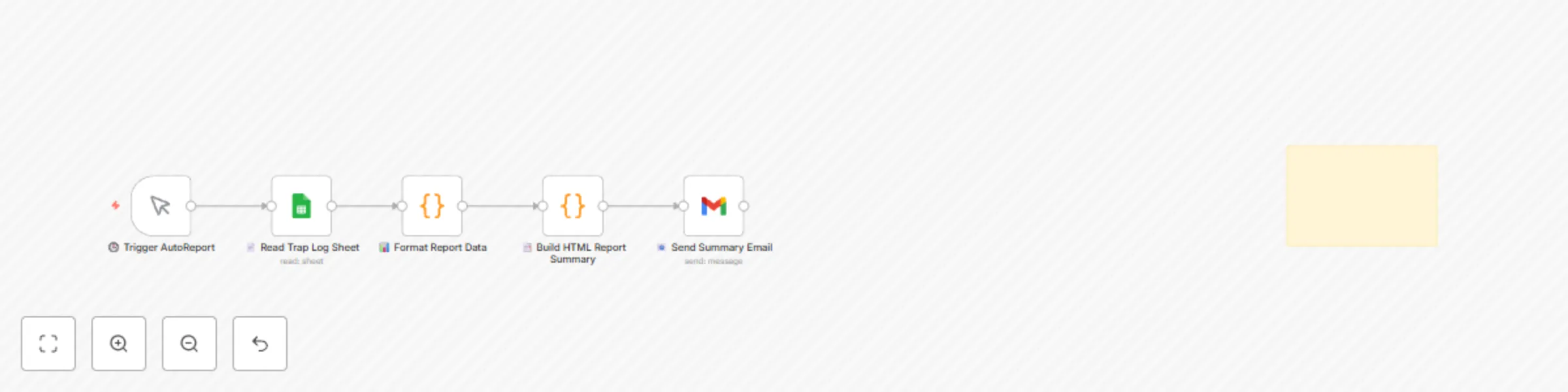
CYBERPULSE AI RedOps: generate daily RedOps security simulation reports
Description Automatically compiles a daily HTML report of all RedOps simulations (Modules 1–5), summarizing offensive...
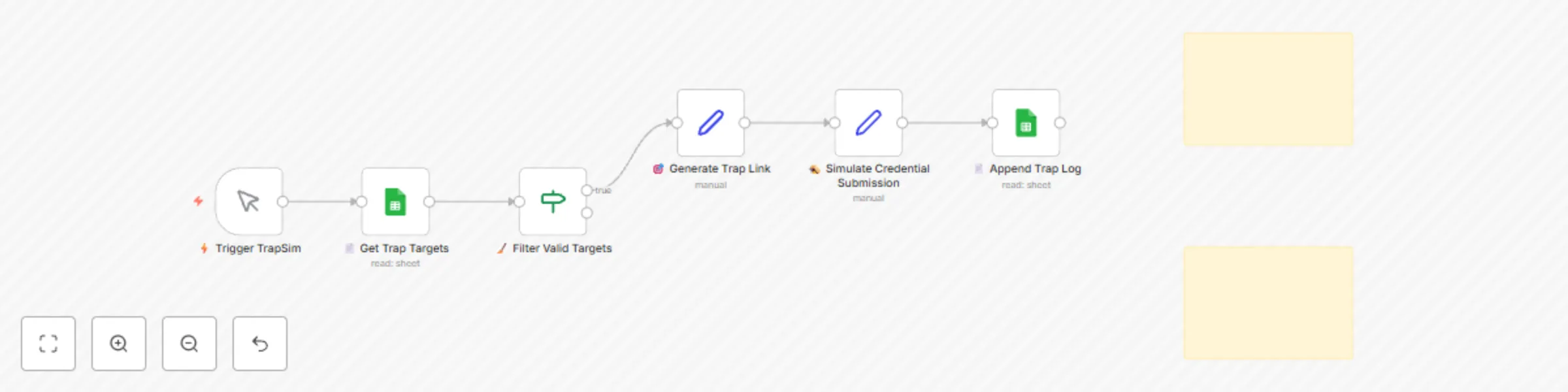
CYBERPULSE AI redOps: credential trap sim: fake login page simulation
📝 Description: Simulate a phishing login page to test user behavior and SOC response. This controlled workflow sends...
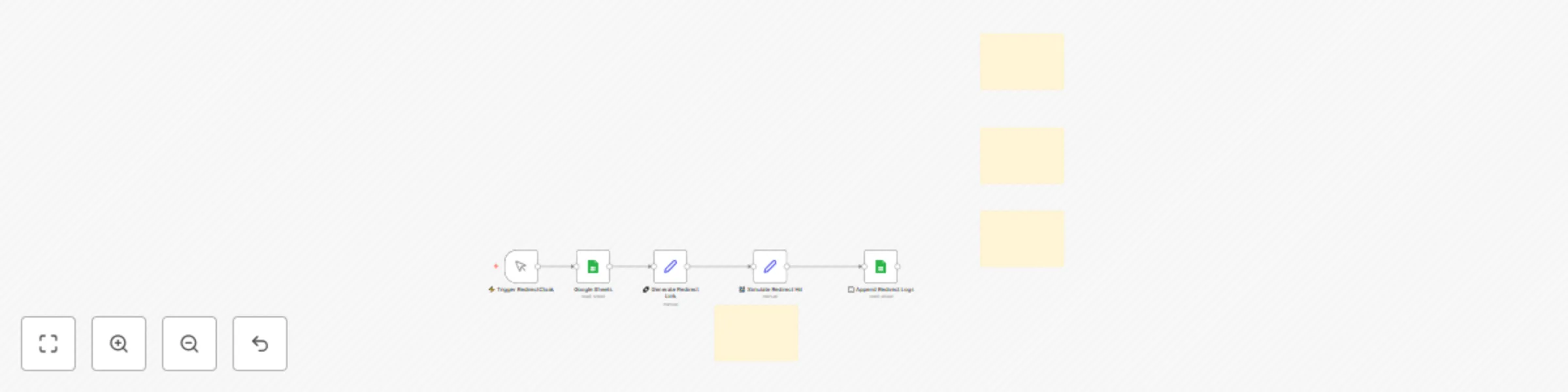
CYBERPULSE AI redOps: phishing simulation with redirect tracking
Description: Simulate cloaked phishing links that redirect through a controlled proxy. This module tracks if secure e...
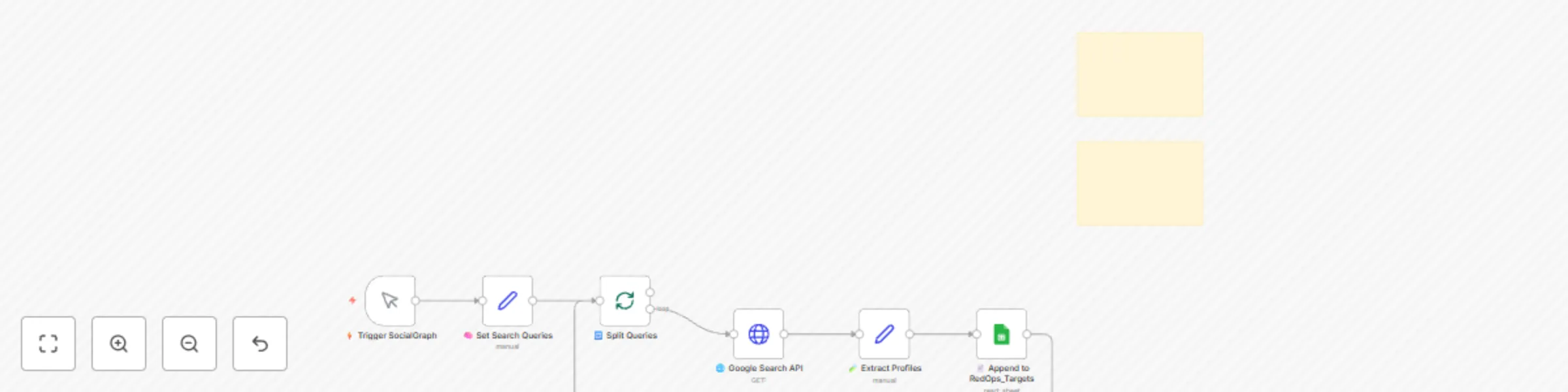
CYBERPULSE AI RedOps: Role-based LinkedIn profile discovery with Google OSINT
Description: Automates public profile discovery for CISO, CEO, and other key roles using Google Programmable Search....

CYBERPULSE AI RedOps: validate email security gateways generated payloads
Description: Automatically send structured benign payloads (PDF/HTML/JS markers) to test email gateways and sandbox r...
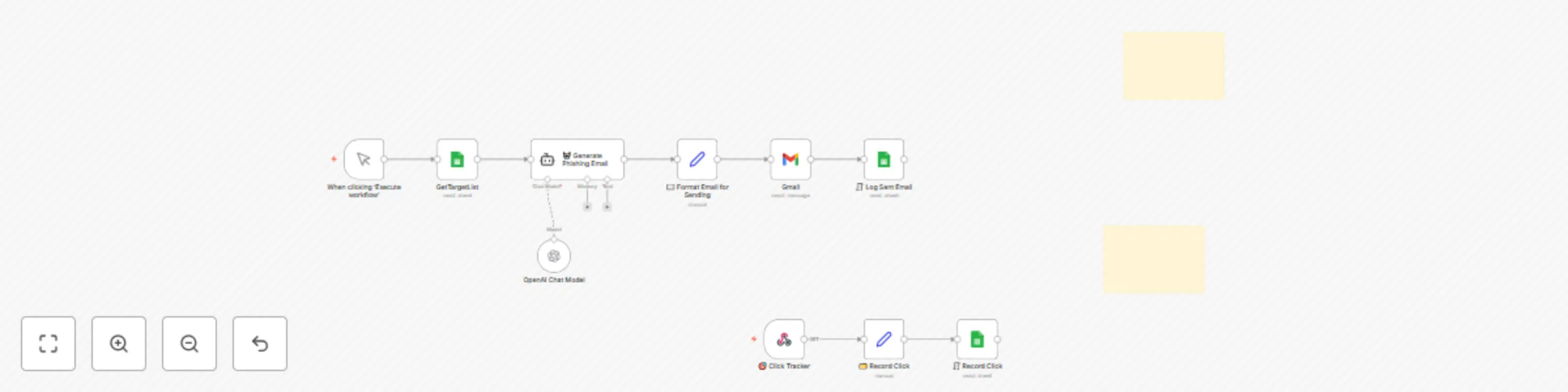
CYBERPULSE AI RedOps: internal phishing simulation for security training
Description: Simulate phishing awareness campaigns using OpenAI generated emails. Send to target lists, log clicks wi...
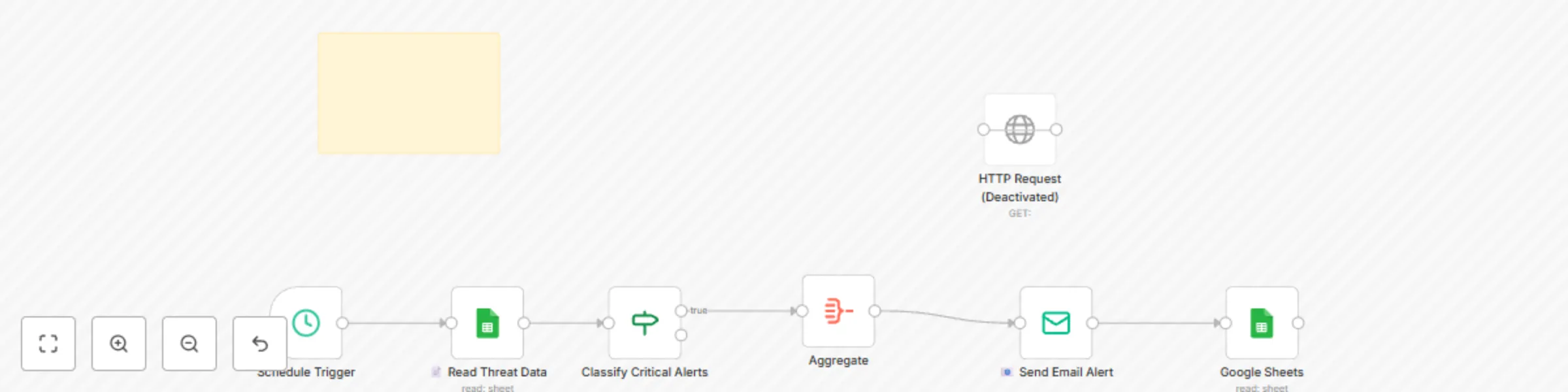
Real-time security threat dashboard with Google Sheets, AI risk analysis & email alerts
👤 Who it’s for Blue Team leads, CISOs, and SOC managers who want automated visibility into threat metrics, endpoint...
Automate security incident response with Google Sheets, email alerts and EDR isolation
👤 Who it’s for SOC teams, incident responders, or solo defenders who need to automatically act on critical threats w...
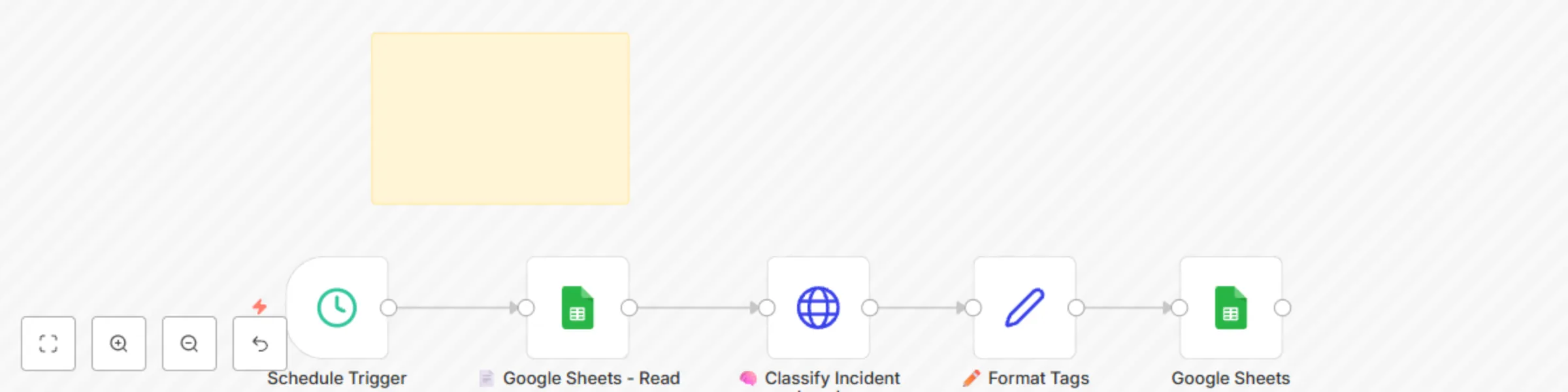
Auto-classify security incidents with GPT-4 and Google Sheets for SOC teams
👤 Who it’s for Blue Team leads, SOC analysts, and IT responders looking to automatically classify security alerts us...

Aggregate endpoint security risk scores with EDR, vulnerability data & Google Sheets
👤 Who it’s for Security teams, SOC analysts, and small to mid IT teams looking to automatically assess endpoint risk...
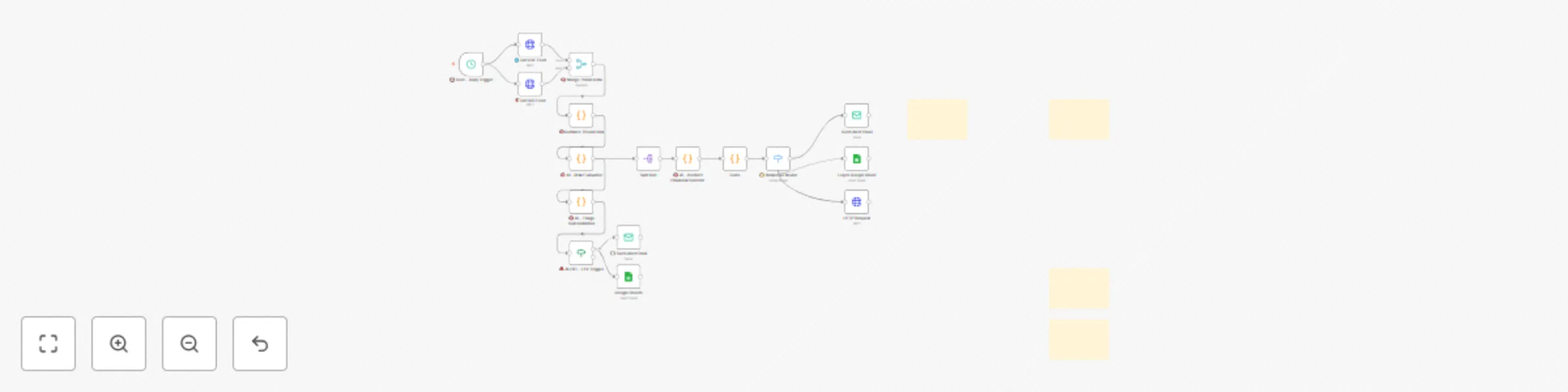
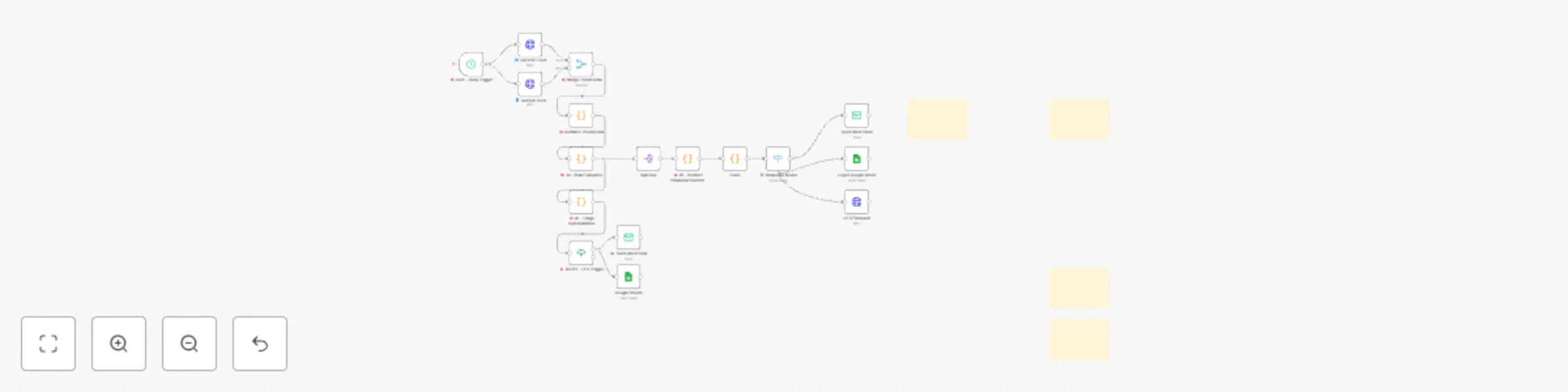
CYBERPULSE AI BlueOps: asset enrichment engine
👤 Who it’s for Blue teamers, SOC operators, cyber analysts, and SME defenders who want to automatically enrich daily...
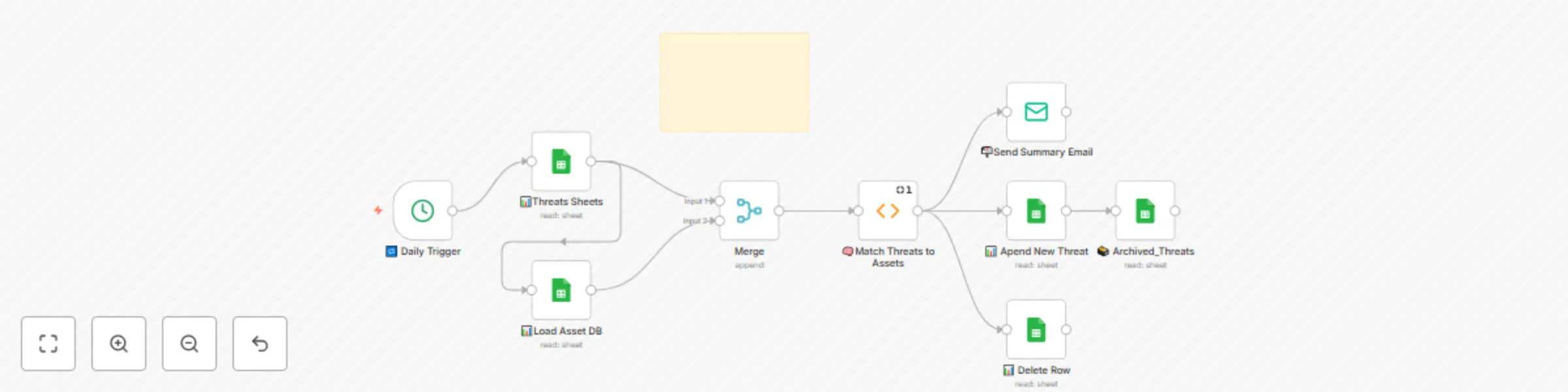
Auto CVE & IOC feed ingestor with OpenAI risk triage & email alerts
How it works This Blue Team workflow ingests threat intelligence from public CVE and IOC feeds, merges the data, perf...
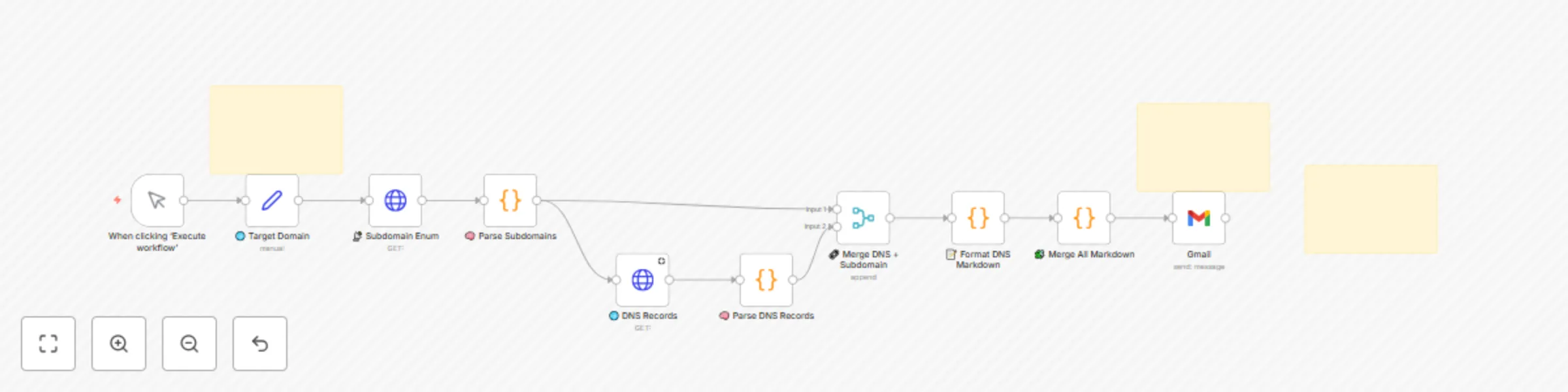
Automated DNS records lookup for subdomains with HackerTarget API reports
🧠 EnumX: Auto DNS Lookup for Subdomains with Markdown Export Who’s it for Security engineers, red teamers, or automa...
AI-powered vulnerability scanner with Nessus, risk triage & Google Sheets reporting
🛡 CyberScan – AI Powered Vulnerability Scanner with Nessus, OpenAI, and Google Sheets 👤 Who’s it for Security teams...